Consequently, the Dark Web as we recognize it today started to take shape, with websites and services specifically designed to operate within this hidden network. It aimed to provide online privacy by routing internet traffic with a series of volunteer-operated servers, encrypting the data at each step, and making it challenging to trace the user’s identity. The history of the Dark Web is intricately tied to the development of internet technology and the ongoing pursuit of online anonymity. Laws vary by country, and while browsing the dark web is not inherently illegal, participating in illegal activities is a crime. However, none provide the same coverage or reliability as surface web search engines, so users often rely on forums, directories, and community recommendations to find trustworthy sites.
Other Ways To Access Dark Web Platforms
Since its public release, researchers have discovered various vulnerabilities in Tor, which have been quickly patched. It derives its name from the encryption system, which is structured like the layers of an onion. The exit node knows where you’re going, but not who you are. The middle node neither knows who you are nor where you’re going. To put it less technically, the entry node knows who you are but not where you’re going.

VPN Over Tor

A VPN will mask your location and stop the online breadcrumbs that can lead back to you. If you need to access dark web resources, these are the steps you need to take. There are many legitimate uses for dark web services and communication. Drugs, weapons, and stolen IP and data are all hot businesses on the dark web, with terabytes of information on offer. When the dark web is mentioned online, it is usually in tandem with criminal marketplaces and arrests made by law enforcement agencies.
Start The Tor Browser

Onion sites aren’t really dangerous, but they could be when accessed through unfamiliar or suspicious links. However, you should not see it as an opportunity to engage in illegal activities to avoid trouble with authorities. The Camouflage Mode is intended for people living in countries with heavy internet censorship, like China. This is high-level protection; no one can intercept your data or activities.
- While the Tor Browser does an excellent job of protecting your privacy and anonymity, you really shouldn’t use it as your daily driver browser.
- With rising online privacy concerns in the current digital age, the Tor network’s anonymity is becoming essential.
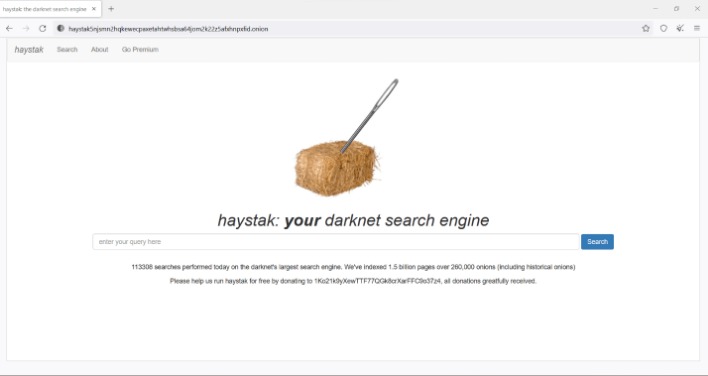
- Offers an extensive archive of dark web sites, with both free and premium versions.
- The site had only been up and running for about seven months, but surprisingly, it gained over 215,000 users.
- Hackers spend a lot of time on the dark web, and it's not too difficult to get access to hacking tools and data leaks in this part of the internet.
There’s a significant risk to dark web users of being exposed to malware (malicious software) infections. These high levels of anonymity increase the opportunity for the “bad guys” to sell drugs, stolen IDs, credit cards, weapons, and many more compromised products or information. It’s no secret that the dark web can be a tricky and dangerous place for the general internet user. Simply download the file, install the software, and you’re ready to use its web-based interface.
Functioning as a modified version of the widely recognized Mozilla Firefox ESR, its core purpose is to facilitate access to the Tor network. Without a VPN, your ISP can see that you’re using Tor, and the first Tor server (entry node) can see your real IP address. While tools like the Tor Browser offer strong anonymity, things like downloading files, enabling JavaScript, or logging into personal accounts can expose your identity. Finally, it lets you appear as if you’re browsing from a specific country (the country the VPN server you’re connected to is in).
Guide To Accessing Tor Via Tails OS On A USB Thumb Drive:
For safer browsing, it is highly recommended to also use a VPN and antivirus software. However, remember you must use the Tor browser to access them. You can choose the best darknet (.onion) website that suits you and start surfing. If you choose to visit the dark web, you must take the necessary measures to protect your privacy and security.
Step 5: Find Verified Onion Links
It’s designed for secure, decentralized storage and is often used for file sharing and accessing information anonymously. Hyphanet (formerly Freenet) is another anonymous network that allows you to share and retrieve information without censorship. For advanced users, I2P offers configuration options for adjusting bandwidth limits, adding encryption layers, or even setting up your own eepsites. Although it’s not as widely used as Tor, I2P can provide robust anonymity and is well-suited for peer-to-peer file sharing. While Tor is the most common method for accessing the dark web, I2P and Hyphanet offer alternative options for secure and private browsing. Dark web sites via Tor have unique URL structures that end in .onion.
- If you're having trouble connecting to the Tor network, try one of these.
- It doesn’t track your IP address, search history, and other personal data.
- These servers support P2P activities no matter where you are.
- On the dark web, you’re expected to find illegal and prescription drugs (including Marijuana).
- The Tor browser is a popular way for internet users to visit dark web sites.
- Fraudulent activities on the dark web include phishing scams, fake identity sales, and the sale of fake products.
How To Use The Tor Browser & Stay Safe: Full Guide 2025
It's a network of volunteer-run servers (called nodes) designed to mask your identity online. Whether you're a journalist, an activist, or simply someone who values privacy, Tor can give you an unprecedented level of online anonymity. For added security, use a separate device or virtual machine (VM) when accessing the dark web. Certain activities on the dark web are illegal in many countries.
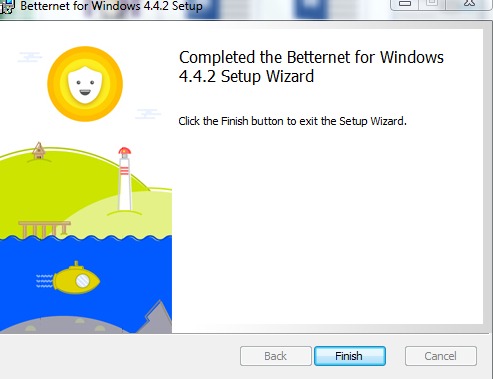
The VPN encrypts your traffic and hides your IP address so that on the surface web, your information is kept private. So, it’s worth using Firefox if you’re up for the tweaks needed. All traffic must always go through the Tor network through the Gateway.
You can now start surfing the web while connected to the Tor network. While Tor is legal in most countries, it can also be used for illegal purposes. Plus, some people still don’t know how to get and use the Tor browser, despite it being pretty accessible and user-friendly. It's the tradeoff for the anonymity Tor provides. However, it's important to understand that your actions online always must comply with the law, even when using Tor.
The dark web is infamous as a dangerous place, where drugs are bought and hitmen hired, but it can be a safe way to browse the internet if your privacy is serious concern. Justice has acquired extensive content writing experience over the years. Justice Ekaeze is a freelance tech writer with experience working for specialized content agencies. While you can’t install the Tor browser from the official website, Chromebook users can configure it via a few simple Linux commands.
On the other hand, it is illegal to use the dark web for criminal purposes or to obtain illegal content. It facilitates access to select dark web content through global proxy servers. The network database is dispersed across nodes and shielded with encryption.

Tor Browser
Use Tor alongside a VPN to ensure your web traffic is fully encrypted. And at the exit node, your decrypted traffic is vulnerable to interception. Anyone who owns and operates the entry node will see your real IP address. Plus, Tor cannot protect against tracking at the entry and exit nodes of its network.
However, using the Tor browser for illegal acts is possible since the network has increased anonymity. Combined with the browser, it will provide maximum security and anonymity online. As a result, monitoring your online data or using it to track you is nearly impossible. This so-called “Tor over VPN” set-up adds an extra layer of security, which can be especially important on monitored or public networks. Tor offers strong protection against network surveillance and website tracking, but without a trusted VPN, your ISP or network admin may still see that you’re using Tor, and your real IP address could be exposed. This segmented design makes it extremely difficult for any observer, whether it’s a website, ISP, or malicious actor, to trace your traffic back to you.



