
Malwarebytes – all-in-one cybersecurity protection always by your side. Voluntary retirement, or “sunsetting”, is second to “exit scam”, which is where the market admins pull the rug from under their clients and partners and run away with the money. Then to round off the year, ToRReZ Market, a site selling illegal products, closed in December 2021. Then in November 2021, Cannazon, the largest marketplace for buying marijuana-based products, shut after a DDoS attack. It’s believed that the administrator behind Joker’s Stash came away a “Bitcoin billionaire”.

A distinct set of sources documents attackers moving beyond simple card-number resale toward active cash-out methods, notably an NFC relay tactic labeled “Ghost Tap” that enables attackers to remotely use stolen credentials by bridging proximity-based payment systems and exploiting mobile-wallet trust chains . Tech researcher and writer with a passion for cybersecurity. After more than a year of no updates, the site admin shut it down, reasoning that he couldn’t keep the list of onion links up-to-date.
Best Threat Intelligence Platform Vendors: Enterprise Buyer's Guide
The best thing is to actually understand how to find the fresh, new links. Hence, you never know when a popular .onion site is going to vanish, or even die. The biggest and most frustrating part about dark websites is that they live for a short span of time. This .onion link makes it impossible for hackers to impersonate your profile. That is why the explorers post their content on the dark web forums rather than the surface web.
Cyble Partner Network (CPN) Join Us
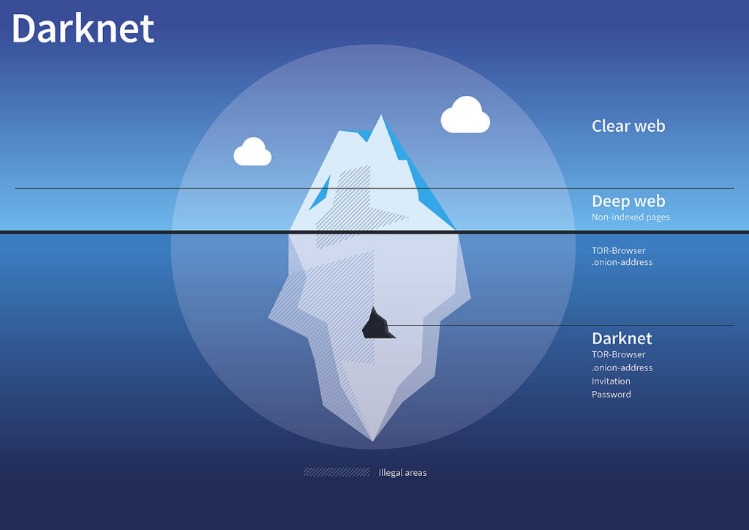
In fact, researchers at Newcastle University estimate that an attack like this could take as few as six seconds. Clever hackers can significantly cut down how many numbers they need to guess and check to find your payment card number. This high barrier entry to the Dark Web exists to protect user identities, online activities and location, and maintain their anonymity. Tracking this activity can be challenging, as dark web marketplaces and communication channels are regularly influx and hidden. Cybercriminals are using the dark web as a means of exchanging stolen or falsely branded assets belonging to legitimate retail organizations.
Accessing Onion Sites On Android
The use of Tor and other privacy-focused tools ensures that users can access these platforms without compromising their anonymity. The demand for pharmaceuticals on darknet markets remains high, with a focus on prescription medications, nootropics, and performance-enhancing drugs. The integration of cryptocurrencies like Bitcoin and Monero has further enhanced the reliability of these markets, offering users a seamless and anonymous payment method. In 2025, darknet markets continue to provide a secure and efficient platform for the trade of pharmaceuticals and digital products.
Use The Tor Browser
Some markets are invite-only or have strict registration rules to keep out scammers and law enforcement. Believe it or not, some dark web marketplaces have pretty advanced systems for building trust. One of the most common is the exit scam, where a marketplace suddenly disappears and takes everyone’s money with it.
Investment Fraud Lawyers At Bakhtiari & Harrison
- This by itself can sometimes be used to make purchases but some people will buy card writers and actually turn a blank credit card into a stolen credit card.
- Freshtools has some characteristics that help it stand out from the other dark web stores.
- Awazon Marketplace is the leading dark-web marketplace that claims to provide a secure destination for anonymous trading.
- In 2025, the landscape of darknet markets continues to evolve, offering users enhanced security, reliability, and accessibility for drug trade.
- In the summer of 2003, separate US secret service and FBI investigations led to the arrest the top administrator Albert Gonzalez of the large ShadowCrew, turned informant as a part of "Operation Firewall".
Adding fullz to a card purchase increases the price by about $30 for a physical card and under a dollar for digital card info. Card smart, card silent. Now that you know what makes a site cardable, let’s get to what you came for.
Blockchain.info (now Blockchain.com) is a popular cryptocurrency wallet and blockchain explorer service (one of the first sites to launch on the dark web). Right now, you can use many cryptocurrency .onion sites to buy or sell all types of cryptocurrencies. The Mailpile .onion site can download information anonymously from any server or web service like Gravatar.
Which Is Better — Tor Over VPN Or VPN Over Tor?
These markets have also improved their user interfaces, making navigation and product discovery more intuitive. Digital products, such as e-books, software, and online courses, also play a significant role in the ecosystem, catering to a diverse audience. The use of cryptocurrencies like Bitcoin and Monero remains central to the darknet ecosystem, providing anonymity and reducing the risk of financial tracking. In 2025, the darknet continues to serve as a hub for secure and efficient drug trade, with platforms evolving to meet user demands for privacy and reliability. These markets prioritize user anonymity, integrating features like multi-signature wallets and decentralized hosting to mitigate risks.
Gangs On The Dark Web: Credit Card Scammers – VICE
This dark web monitoring will help you track illicit activities and minimize the risks of cyber-attacks. Note that engaging with the content in any way is not only distressing but could also put you at legal risk. That is why you should only use a reliable VPN like ExpressVPN or NordVPN for additional security and privacy. While Tor offers anonymity on the dark web, your online activities leave breadcrumbs that can reveal your identity. Many dark web sites offer malware as a tool for cyberattacks. Accessing blocked content can result in being placed on a watch list or imprisonment.
The Hidden Costs Of Illegal Streaming And Modded Amazon Fire TV Sticks
If you’re in a coffee shop or anywhere else you don’t trust network security, use a virtual private network (VPN) to encrypt all communications. According to a report published by cybersecurity company NordVPN, the country is third only to the United States and India. Onion sites are “crawled” and added to the list provided their “robots.txt” file permits it, and if it is not on their blacklist of sites with abuse material. Some card issuers offer identity protection to cardholders, and others offer it to anyone and everyone. People can’t keep their information off the web due to professional reasons, and many processes are exponentially more convenient through an online profile.

Fraud Protection And The Dark Web’s So-Called ‘Carding Industry’

To find .onion links for dark web sites, you’ll need to use a dark web search engine. It’s made up of forums, marketplaces, and websites you can’t find with a Google search and requires specialized software to access, such as the Tor Browser. The best news is Torch updates its sites every single day, so you’ll always be able to browse the latest news and access new services and sites.
At the dark end of the web, you’ll find the more hazardous content and activity. However, you can still take illegal actions within Tor that could incriminate you regardless of the browser’s legality. For instance, machine learning has shown time and time again that advanced technology can detect patterns that fraudsters aren’t aware of.
Telegram channels supplement traditional onion sites, blurring lines between the dark web sites and more mainstream communication tools. Despite growing crackdowns from law enforcement agencies, the dark web remains a hotbed of criminal activity, offering everything from drugs to stolen data. Comparitech researchers sifted through several illicit marketplaces on the dark web to find out how much our private information is worth. Because it’s for a low amount, the test transaction is less likely to set off a card issuer’s fraud detection or be noticed right away by the cardholder. These sites are often used by cybercriminals to monetize data breaches and other forms of cybercrime.
- It is also used by whistle-blowers, journalists, and other individuals who are not involved in illegal activity but need to protect their communications and identities.
- Torzon is one of the most notable dark web stores for a number of reasons.
- Forged documents like driver’s licenses, passports and insurance cards can be ordered to match stolen information, Privacy Affairs said.
- To protect yourself, avoid sharing personal or financial information online, use strong security measures for your devices, and remain informed about common online scams.
- As always, use Tor Links with care, as it includes onion links to dubious or illegal activity.
- First, well, they had access to his e-mail so they could see any flight plans he had and all this kind of stuff.
If you want to reinforce the security of your primary email accounts, you can easily set up a separate email account for all unimportant online accounts. MFA should be an integral part of our online security at all times, not only when we’re faced with a breach. The dark web is a part of the internet that is not indexed by search engines and is only accessible through special software like the Tor browser.
A data breach can result in significant financial losses, damage to your reputation, and potential legal action. The data is usually sold in bundles, with the price depending on the amount and type of information available. Recently, on February 17, 2025, Dark Web Informer claimed that B1ack’s Stash is a “legitimate” fraud site. DarkOwl analysts discovered a well-known dark web research website called Dark Web Informer, which also mentioned B1ack’s Stash twice on its Telegram channel. Most comments range from negative to neutral, while very few users gave clearly positive endorsements based on their site experience. B1ack’s Stash’s sudden rise in popularity has been met with mixed reactions from dark web users.
You can access it with regular web browsers and search engines. It means you cannot access websites on the dark web with regular browsers like Firefox or Chrome. Some markets even sell privacy tools, but you are more likely to run across counterfeit prescription pills and stolen identities. As such, we do not recommend using Tor if you want to do data-intensive activities like streaming in HD, gaming, torrenting, or making video calls. This network of over 6,000 relays hides your location, thus protecting you from online surveillance and third-party tracking by your websites.
Hackers have their tricks to exploit public Wi-Fi networks and use these unsecured networks to distribute malicious software, gather data, carry out man-in-the-middle attacks, and much more. While some use it to evade government censorship, it has also been known to be utilized for highly illegal activity. The threat actors claim that at least 27% are still active, but it is unclear if that is true.



