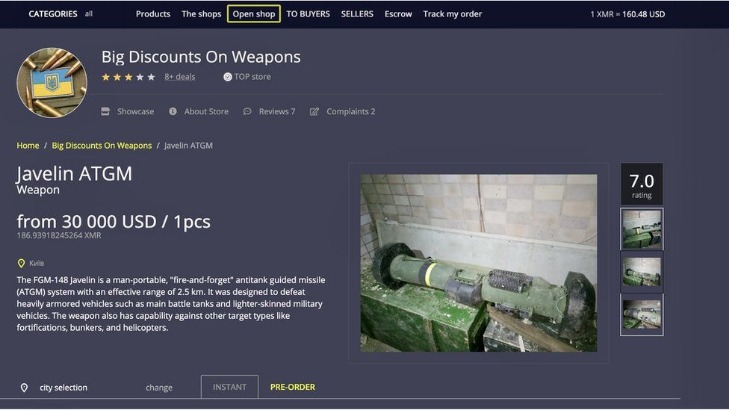
Immediately after a big takedown, users flood to remaining markets or spawn new ones a whack a mole cycle. It specialized in narcotics fentanyl, heroin, cocaine, stolen financial data, fake documents, and even in house money laundering/mixing services. It specialized in narcotics, stolen data credit cards, credentials and contraband. Silk Road’s demise proved that even Tor hidden sites could be penetrated by good detective work, prompting many users to flee to successor markets. These markets use cryptocurrencies and encryption to hide, but law enforcement’s growing technical skills have repeatedly broken them open.
Request A Demo To See How Cyble Helps Organizations Strengthen Digital Defense!
The dark web comes with its own set of tools and services, including web browsers and search engines (which I'll get on to in a moment). It accounts for around 90 percent of websites, by some estimates, so we're talking about a substantial chunk of everything that's online. You'll often see these terms used in your travels across the internet, and there's some confusion about what they mean. It's a part of the internet that's less regulated and more shadowy, for better and for worse. The dark web, for the uninitiated among you, is a virtual neighborhood beyond the borders of the normal, everyday internet (which includes the website you're looking at right now). You probably don't want to access any of the websites where any of this stuff can be bought.
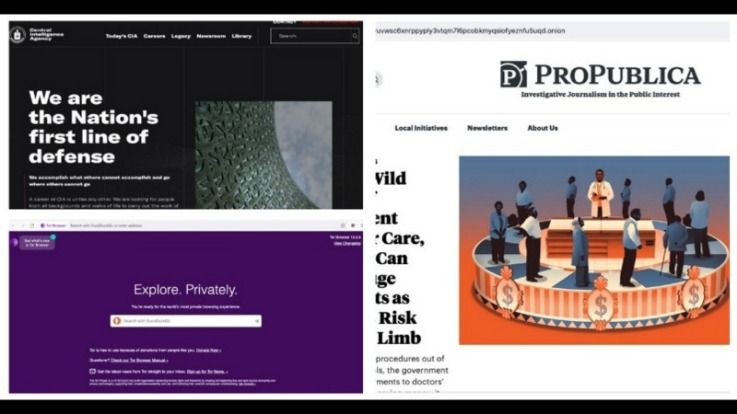
Although content on the dark web is not as ‘indexed’ compared to the one on the clear web, you can still use search engines to find stuff. For this tutorial, I’ve used Universal. Chill, because nobody will ever find a record of you ever fiddling around the darknet. I recommend using a stick since DVDs have a read-only function after you’re done burning well and accessing the dark web required a bit of writing. It’s like in those movies where the doctors are experimenting on deadly viral strains from behind the safety of a glass enclosure.

However, it is important to note that no security measure is foolproof, and engaging in illegal activities on the Dark Web can have severe consequences. It routes your internet traffic through a network of volunteer-operated servers, making it difficult to trace your online activities. Next, let’s explore how individuals can access the Dark Web safely, while minimizing personal risks and vulnerabilities. Prioritize online security, protect personal information, and consider the legal and ethical implications of participating in illicit activities.
What’s the difference between classic marketplaces and data stores? Regardless of your jurisdiction, activities such as trading stolen financial data, compromised accounts, or money laundering services are illegal. Abacus Market offers an extensive array of illegal goods and services across various categories, making it one of the most versatile marketplaces on the dark web. Our team searched the dark web and put together a list of the most active dark web marketplaces in order to assist you in monitoring illegal trade of products, cybercrime activity, and dark web trends in the dark web space.
Step 9: Maintaining Security And Privacy
These illegal activities are made possible by the layer of anonymity provided by Tor and other similar networks. These markets host hundreds, or in some cases thousands, of people who sell drugs, commonly referred to as “vendors”. Hackers spend a lot of time on the dark web, and it's not too difficult to get access to hacking tools and data leaks in this part of the internet. However, there are plenty of legal and legitimate online activities that require privacy and anonymity. LegitScript's investigative analysts frequently conduct research on both the surface web and dark web in our efforts to identify operators illegally selling drugs and other federally regulated products. These dangers exist on the surface web as well; however, without illicit marketplaces that have built-in escrow and rating systems, there may be a higher likelihood of nondelivery schemes and phishing scams from websites on the surface web.
It is important to remain informed about emerging threats and actively participate in efforts to enhance cybersecurity. It can result in financial losses, reputational damage, and invasion of privacy for those whose data has been compromised. Buyers can acquire personal information and financial details without revealing their identities, giving them the means to engage in criminal activities without being traced.
Simply accessing the dark web and using the Tor browser may already raise government suspicion. Anyone can access the dark web, and it’s not that complicated to do so. Tails always starts with a clean slate and any evidence of the activities you engage in while using Tails disappears when you shut down Tails. The advantage of using a dedicated computer just to browse the dark web is that your main computer isn’t exposed to any of the threats or risks tied to entering the dark web.
Minimize Or Rescale Your Tor Browsing Window
By following these steps, you can ensure a higher level of anonymity when making payments on the Dark Web. Scrub any metadata from files or documents before sharing or uploading them. Avoid using payment methods that require such information, as they can compromise your anonymity. These services help obscure the transaction trail by mixing your Bitcoins with those of others, making it challenging to trace the origin. Protecting your anonymity during the payment process on the Dark Web is crucial.
Additionally, individuals may face remorse and guilt for contributing to financial fraud and identity theft. This renders them useless for fraudulent activities, leading to a loss of investment. Stolen credit card details may have limited validity or already be canceled or blocked by the issuing banks.
Dark Web Search Engine

Her background in computers and information security gave her an advantage when it came to navigating the dark web. She had never purchased drugs in the conventional way—and, at the age of 28, still hasn’t. Marie had never purchased drugs in the conventional way—and still hasn’t. He no longer likes buying from the streets of New York, as he did when he began using heroin in the 1990s, because of the risks he experienced in certain neighborhoods. With all that said, it’s best not to buy anything from the dark web as it can be dangerous, and it’s almost always illegal.
History Of Dark Web Marketplaces
Other dark web search engines worth investigating are Ahmia, Torch, NotEvil, and the Onion URL Directory—just type out some keywords for what you're looking for. Many people install a VPN as well, but then you're putting your trust in an additional third party to not track your activities or report them to anyone else. Bear in mind too, that your internet provider will be able to see you connecting to Tor nodes, even if it doesn't know exactly what you're doing. It blocks trackers, prevents user fingerprinting, encrypts data, and reroutes your browsing so no one can see where in the world you are. Tor is a browser engineered for extra security and privacy, and can be used to navigate the normal, surface web as well as the dark web. Part of what makes the dark web the dark web is that you can't access it through your normal web browser, nor can you look something up on it via a Google search.
- “The more we understand how guns move, how they are sold, and what types of guns are available on the dark web, the more we’ll understand how the internet can serve as a niche market for gun distribution.”
- The website allows visitors to view all the goods and services on display before they buy something.
- There are a lot of misconceptions about the dark web online and in popular media.
- Rather than focusing on premium access, it thrives on low-cost, high-volume sales.
- Many users value the protection that comes with keeping their identity hidden.
This makes it difficult for interlopers to monitor the traffic or trace any legal or criminal activity back to you. This essentially means that over 93% of Tor daily users use the dark web for legitimate reasons. However, using the dark web for illegal activity can be a criminal offense.
Cyble Titan Endpoint Security
Remember to remain responsible, respect legal boundaries, and prioritize ethical conduct throughout your Dark Web activities. By following these steps and staying vigilant, you can better safeguard your security and privacy while engaging with the Dark Web. If necessary, use a reliable VPN to encrypt your internet traffic when connected to public Wi-Fi. Use a password manager to securely store and manage your passwords.
This anonymity makes it challenging for law enforcement agencies to track down the culprits and shut down these illegal operations. The potential profit from these illegal activities is enticing, especially given the relatively low cost of purchasing the credit card information. The Dark Web provides a platform where fraudsters can monetize stolen credit card information, posing a significant threat to individuals and financial institutions alike.
These cryptocurrencies offer additional layers of anonymity and privacy, making them attractive alternatives for certain transactions. Bitcoin transactions are conducted through digital wallets, and the transactions are recorded on the blockchain, ensuring a high level of security and privacy. Due to the anonymity provided by the Dark Web, traditional payment methods are often not acceptable.
Its fall disrupted a huge part of the global drug trade, showing that even sprawling, language specific markets can be dismantled. This set the legal precedent that even Tor hidden markets are prosecutable. Each takedown from Silk Road to Archetyp has shown that anonymity on Tor is fragile against determined investigators.
Download And Install Tor
Its commitment to privacy, diverse product offerings, and robust security measures make it a preferred choice for users seeking discreet transactions within the darknet. Established in 2022, Torzon market is one of the biggest and most diverse marketplaces on the dark web. Established in 2019, Russian Market is a well-known and highly regarded data store on the dark web, specializing in the sale of PII and various forms of stolen data. It has built a reputation for being a reliable source of stolen credit card data and PII. It is a hub for financial cybercrime and offers a wide range of illicit services and stolen data that cater to sophisticated cybercriminals. Beginning in September 2021, Abacus Market has established itself as one of the leading dark web marketplaces.



