Unlike traditional search engines, it organizes dark web links into specific sections, making it easier to navigate and explore different parts of the dark web. While not strictly a search engine, OnionLinks provides a directory-style resource that helps users discover various .onion sites across different categories. It uses a freemium model and offers several features for premium users like access to historical versions of websites. WormWeb is a user-friendly search engine built specifically for the dark web, providing quick and easy access to .onion websites.
Best Tor Websites In 2025

Over 6,000 relays in this private network ensure nobody will find out where you are from. Through volunteer-operated nodes, it passes internet traffic throughout the world. However, they are created using a cryptographic accessible via Tor only. It indicates strict protection for all user data and no government eavesdropping. Usually, domain names for darknet sites consist of a random combination of characters and symbols— it is difficult to find them.
Mozilla Firefox can access Tor if you configure it to use a Tor SOCKS proxy, but it’s not built for Tor’s threat model. This platform is ideal for peer-to-peer services, anonymous publishing, and apps that need persistent, distributed hosting. It uses different addressing and protocols than Tor, so .onion sites usually won’t work on I2P. Avoid clicking on random links shared on social media, chat apps, or marketing sites. Reputable platforms like SecureDrop and ProPublica publish official .onion domains for safe access. You need special software like the Freenet or Tor browser, which uses onion routing to encrypt data across multiple nodes.
Is Accessing The Dark Web Legal?
Whereas the deep web is the part of the web not searchable by traditional search engines and requires special tools to access it. You can access it with regular web browsers and search engines. It means you cannot access websites on the dark web with regular browsers like Firefox or Chrome.
What Is Candle Search Engine?
Users have access to settings that allow them to control search parameters and privacy settings, further enhancing the personal security and customization of the search process. Unlike other search engines that create profiles of users to target advertisements, DuckDuckGo does not track clicks or searches. Founded in 2008 by Gabriel Weinberg, its mission is to offer a more private alternative to the search engines that dominate the market, which often collect and use personal data for advertising purposes. Categories might include but are not limited to, secure communication services, marketplaces, financial services, and whistleblowing sites. It compiles links to different websites on the dark web, ranging from forums and marketplaces to libraries and blogs. Unlike the surface web, which is indexed by popular search engines and easily accessible, the dark web requires specific tools and knowledge to navigate.
What To Do If You See Something Illegal
Many people see hacked information and stolen card data being sold on the dark web. The dark web also helps individuals communicate about or sell illegal items such as weapons, drugs, malware, etc. An easy way to find content on the dark web is to receive a link from someone who already knows about it. Lastly, the dark web is the portion of the deep web that is generally inaccessible and is much larger than the surface web. As a result, you cannot find them with a regular search engine.
Hidden Answers
The last item on our dark web websites list is Google Feud or rather its evil twin. Browsing the dark web without caution may lead to hazardous outcomes, such as being redirected to other URLs, fraudulent websites, or scams. Apart from having that “As above, so below” vibe, Tunnels is a great source of info for users who are into dark urban history. Careful though, because many ‘users’ reported malicious links and redirects while perusing Sci-Hub.
Politicians, leaders and other categories of users have found shelter within it. The name dark web has been synonymous with anonymity. This medium can be used to exhibit contents which are otherwise legally barred. The principle of maximum-security laid foundation during this time.
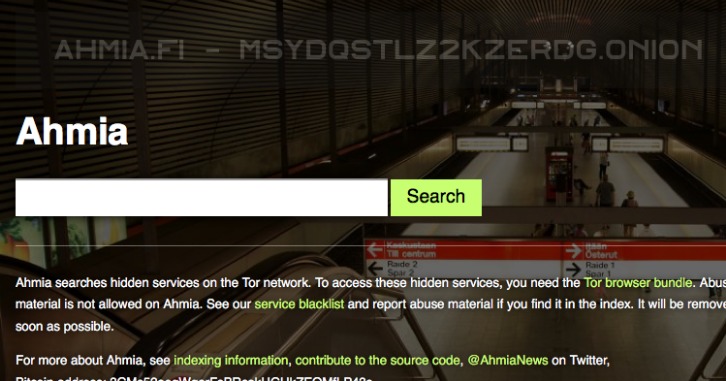
It has a reputation for being fast and effective, though the content it indexes varies widely in quality and legality. It also promotes transparency and security by openly sharing its source code and inviting contributions. And unlike the regular web, you can’t even access it from a standard browser. Learn how to turn threats hidden in the dark web into actionable threat intelligence. As we enter 2026, these tools are adapting with improved security and functionality to meet user needs.
What Are Onion Links And How Do They Work?
Riseup is an invite-only email and communications service that doesn’t hold onto any of the data you generate when you use it. However, The Wayback Machine allows website owners to block their sites from being archived, while archive.today does not. Although ProtonMail also exists on the clear web, accessing it via Tor provides an extra layer of privacy if you don’t want to leave a trace of you even using ProtonMail. The service retains no copies of any data that passes through a ProtonMail account. ProtonMail is an email service that uses end-to-end encryption, making your email accessible to you and only you.
Other Dark Web Sites Offering Email Services

Some fake sellers take your crypto and never ship what you ordered, or phishing sites that look like real marketplaces but steal your login info. But once you start doing illegal things, like buying drugs or stolen credit cards, that’s when you’re breaking the law. Just visiting the dark web, or using a tool like Tor, isn’t illegal in most countries.
You can execute Whonix inside a hypervisor (VM) and keep the workstation anonymous by design. Unlike Tor, it relies on peer-to-peer connections, and you must install the I2P client to access it. Still, if you’re more cautious about your security, you can try out these advanced tools.
In addition, it is worth noting that users should not blindly trust links on the Hidden Wiki because this is a community resource that anybody can update, and some of the links are malicious. Just remember to proceed with caution because you should only use services you feel comfortable with, and that have a low risk of leading to scams or illicit content. It is essentially a list of all the notable websites available on the Tor Network that is kept in a single, organized place. The Hidden Wiki is one of the easiest ways to find useful resources and websites on the Dark Web. Please note that you must take great care when using the Dark Web as sites often contain adware, spyware, malicious links, and scams.
- Although ProtonMail also exists on the clear web, accessing it via Tor provides an extra layer of privacy if you don’t want to leave a trace of you even using ProtonMail.
- For the record, there are more scam sites for every genuine one, and it’s good to have a discussion forum about this.
- Unlike the surface and deep web, you can’t access the dark web via a standard or specialized search engine.
- If you’re feeling chatty, you can always access a chat room.
- Although the underground internet world is rife with everything bad, it also hosts positive elements.
- Be aware, however, that there are sites for absolutely everything, from the benign to the very illegal.
The merry land of dull websites is what some term dark net as. VPN services provide users with different levels of experience with their helping hands. A VPN helps to anonymize the transfer of data that happens on networks. Therefore, it is necessary to protect your computer and prevent unauthorized access to it using security tools.
Read on to learn more about the five main types of darknet websites and what they contain. Learn more about the kinds of sites that can be found on the dark web and how you can access them. The Tor network provides powerful tools for enhancing online privacy and anonymity, but these benefits come with certain trade-offs. As you discover the hidden depths of the web, ensure your sensitive data remains protected, no matter where it travels. From marketplaces for drugs and weapons to stolen data – the potential anonymity promotes a shadow economy that is difficult for law enforcement authorities to control.
However, data is required for understanding, monitoring, and improving the network. The goal of an anonymous and privacy network, Tor, is not to engage in the extensive collection of data. It collects data from the public Tor network and archives historical data of the Tor ecosystem. Its goal is to offer anonymous access to the content without being censored, no matter where you live. Thankfully, some useful sites can help you circumnavigate the dark web landscape as you search for the best content.
Yes, a VPN adds an extra layer of privacy and security when accessing the dark web, reducing the risk of tracking and surveillance. Whether you're tracking data breaches, uncovering financial fraud, or identifying threat actors, these resources will help enhance your dark web investigation capabilities. This blog introduces the top 21 dark web resources used by OSINT investigators, cybersecurity analysts, and digital forensics experts.
Archive Today’s .onion link allows users to access its web page archiving service anonymously, preserving snapshots of websites for future reference. ProtonMail’s .onion link provides encrypted email services, ensuring privacy and security for users accessing it via the Tor network. The BBC’s .onion link provides secure access to its global news platform, enabling users to read BBC content anonymously, even in countries where the BBC is banned. It began as a simple, categorized directory of .onion links — helping new users find forums, search engines, whistleblowing tools, and more. Dark web search engines help users discover hidden .onion content that isn’t indexed by traditional search tools.



