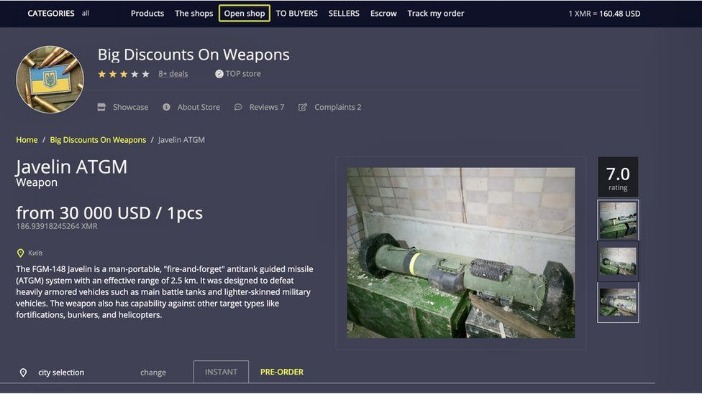
Passwords, tokens, session data, and API keys are valuable commodities on marketplaces. If corporate credentials appear on a marketplace, security teams can quickly revoke access and investigate. Many marketplaces operate like structured organizations, with administrators, moderators, and Support teams. Just like legitimate online marketplaces, dark web platforms rely on vendor reputation.
Threat Intelligence And Monitoring

You can also update permissions to enhance your privacy and keep cybercriminals from accessing your device’s camera, microphone, or location. You can find some dark web directories on the surface web. That is important for those who may fear persecution for their actions or live in areas where access to information is regulated. For example, ProPublica—a renowned investigative journalism non-profit— uses the dark web to communicate with whistleblowers and ensure readers can access content without facing retaliation. Of course, cybercriminals can also use them for nefarious purposes like discussing illegally shared interests, conspiring to commit crimes, or posting content deemed too unsavory for the clear web.
What Kind Of Content Is On The Dark Web?
When data brokers get hacked, the stolen data can include compromised credit cards, social security numbers, and other data, depending on what was exposed in the breach. To check, you can use dark web scanning or breach detection tools like Avast Hack Check or LifeLock Breach Detection to search for compromised data. Lack of regulation by authorities or other users makes it easy for cybercriminals to carry out scams. Regular dark web visitors know that it’s possible to exploit the sketchy reputation of the space and the services offered. Before visiting any dark websites, get comprehensive cybersecurity software to help protect yourself from threats you may encounter. Lastly, The Hidden Wiki is a collection of dark web links — but the links may not work and can lead to dangerous websites.
These search engines neither track your search queries nor record any information, improving digital privacy and keeping your data private. A dark web search engine like DuckDuckGo offers impressive anonymity features and makes it easy to access the shops. Using a dark web search engine is a great step towards enjoying a more secure experience while shopping on the platform. The security level is set to ‘Standard’ by default, but you can change it to the ‘safest’ and enjoy more security while accessing the dark web.
- Launched in 2023, STYX focuses on financial crime, providing stolen credit card data, hacked bank accounts and access to various cryptocurrency laundering tools.
- The subreddit r/deepweb is a good starting point for asking more experienced users about how to search the dark web and deep web for the content you want.
- RiseUp is a top dark web website that offers secure email services and a chat option.
- To access them, you need to use special browsers like Tor, which allow you to browse anonymously.
- As such, they are normally under intense scrutiny from law enforcement and security professionals alike.
- The standard dark web browser is Tor Browser, which directs your browser traffic through the Tor network so you can reach the darknet.
Related Articles From The Safe Browsing Section
Installing the Tor Browser is the best way to access the dark web. Second, shutting down or controlling access to the dark web would be a huge undertaking and could have unintended consequences. First, it’s difficult to track and monitor activity on the dark web since much of it is encrypted. There are many different ways to access the dark web, but navigating it can be tricky and dangerous if you don’t know what you’re doing. Yes, you definitely need a VPN if you want to access the dark web on your phone. This website allows you to type in your email address or phone number and see if it’s been compromised in any data breaches.

How Encryption Keeps Your Purchases Private
If you choose to visit the dark web, you must take the necessary measures to protect your privacy and security. Some of these sites are very helpful (but unseen as Google doesn’t show them), while others are just for fun. It then depends on you, as the user, how you surf the dark world.
Easy Shopping For Quality Products
Once the verified address is secured, users access the market using the Tor Browser, which provides the necessary anonymity by routing traffic through a distributed network. Encrypted lists serve as the primary directory for discovering operational darknet markets, directly impacting the efficiency and security of user navigation. The Tor browser is essential for accessing these .onion sites, as it routes internet traffic through a global volunteer-run overlay network, concealing a user's IP address and location.
Its fall disrupted a huge part of the global drug trade, showing that even sprawling, language specific markets can be dismantled. This set the legal precedent that even Tor hidden markets are prosecutable. These reveal the true scale for example, Hansa’s covert run logged over 38,000 transactions and dozens of thousands of user messages.
Top 10 Dark Web Markets
"They do not curtail the collection of your online activity by your ISP, advertisers, and trackers. They don’t prevent someone monitoring your network from seeing what websites you’re visiting. Tor Browser does." Tor refers to "the onion router", which is a network that bounces your traffic through random nodes, wrapping it in encryption each time, making it difficult to track; it's managed and accessed via the Tor browser. Indeed, Facebook, The New York Times and now even the CIA have sites on the dark web, hosting "onion" versions of their pages that can be accessed via the Tor browser. For example, people like journalists, activists, and academics use it for cybersecurity or research, to access information in regulated countries, and for anonymous whistleblowing.
It uses TrustedServer technology on the entire server network to wipe out your data after every session. Moreover, NordVPN is a service that doesn’t store or log your search results. This means you will get a VPN’s security and enjoy the anonymity of the Tor network simultaneously. Since you are navigating in uncharted territories with all the myriad threats today, you’ll have to disable them in your network settings to stay safe.
Solutions like SAGA® by Munit.io help organizations gain visibility, detect emerging risks, and act quickly when their data, credentials, or brand appear in underground markets. Understanding how dark web marketplaces work helps analysts evaluate the extent of exposure during an investigation. Understanding how dark web marketplaces work helps organizations assess the risks they face. This hierarchy is part of how dark web marketplaces work behind the scenes. Cryptocurrency is central to how dark web marketplaces work. To understand how dark web marketplaces work, you must look at the structure of listings.
As a result, you should avoid opening unfiltered sources, torrent sites, and dark web links unnecessarily and downloading every file you come across. Many dark net sites do not undertake the necessary measures to protect users like most websites on the surface web. To prevent detection, the program runs user data via a tiered stream before allowing access to the dark web. Specifically, the I2P darknet is accessible, while the Tor network is accessible through the Orchid Outproxy Tor plugin. With the onion browser, you can access ordinary HTTPS websites on the web. Some users also share links on encrypted apps like Telegram or Keybase that you can check.

Between 2023 and 2024, the share of new darknet marketplaces accepting only Monero rose from just over one-third to nearly half, reflecting a clear trend toward anti-surveillance tactics, according to Kurrie. The operations are becoming more professional and many platforms mimic legitimate e-commerce sites displaying user reviews, seller ratings, and dispute resolution systems to build trust among illicit actors. “Many cybercriminals are migrating to encrypted messaging platforms such as Telegram, TOX, and Matrix, as well as invite-only forums, reducing their reliance on traditional Tor-based marketplaces,” Salom adds. “In parallel, some actors are experimenting with blockchain-based hosting, decentralized DNS, and peer-to-peer marketplaces, which offer greater resilience against takedowns and surveillance,” Salom says. It’s fragmenting into specialized communities that include credential marketplaces, exploit exchanges for zero-days, malware kits, and access to compromised systems, and forums for fraud tools.
How To Download And Use Tor
Scammers prowl the dark net, launching fake storefronts that vanish overnight, often with their victims’ money. While they look like your run-of-the-mill websites, there are important differences. It is now one of the most widely used browsers to access the dark web. Originally created by the US military to enable secure and anonymous communication, this hidden layer of the Internet has since evolved into a complex digital underground. Social platforms buzz with anonymous conversations, even as law enforcement hunts through digital shadows to crack down on criminal rings.
Immediately after a big takedown, users flood to remaining markets or spawn new ones a whack a mole cycle. These hidden markets promise anonymity, but in practice, users often slip up. Dark web marketplaces are hidden online bazaars on Tor or similar networks where anonymous vendors sell illicit goods. Registration was mandatory to access the Silk Road (like most darknet platforms). Some alternative links are available, providing access to the marketplace. It uses PGP encryption, two-factor authentication, and OPTP authentication to ensure users’ security.