Tor significantly boosts online privacy by encrypting and rerouting internet traffic, but its entry and exit points could be weak spots. In addition to standard websites, there are also servers that are only accessible through the Tor browser. Tor is also regarded as the most user-friendly way to log on to the "dark web," a network of websites that are not visible through standard browsers like Chrome or Safari.
Commercial Services
That way, you can change your passwords and lock down your accounts to help block scammers from using your data against you. Hackers sell access to email accounts, social media profiles, or other information that can be used for identity theft. Fraud and scams run rampant on the dark web, including offers too good to be true and fake services requiring upfront payment. Others sell software exploits that other cybercriminals can use to infect victims with malware and steal personal data. Some dark web commerce sites have dangerous chemicals and weapons for sale. Because of the dark web’s association with illicit activity, your use of Tor may be tracked by your ISP, drawing unwanted scrutiny to your browsing behavior.
- Tor will ask you whether you want to connect directly to the Tor Network or use your own secure connection.
- Most dark web browsers use The Onion Routing (Tor) network, where data is encrypted in layers and sent through multiple nodes.
- Despite this, tracing a specific user's activity on the Tor network is highly difficult and rarely achievable.
- Naval Research Laboratory to protect sensitive government communications.
- The above configurations help improve your security when surfing the web via Tor.
If you make use of a password manager, then it may come with a feature that monitors the dark web for mentions of your email address and password, or any other personal details. Even if you're using a private, anonymized crypto wallet, there are other ways your identity can be revealed—even if it's something as simple as letting a personal detail slip in an instant message. Another private cryptocurrency you'll find being used is Monero, which prides itself on being untraceable.
What Is The Dark Web? How To Use Tor To Access The Dark Web
The dark web is a small section of the deep web that is hidden on purpose, requiring specific software to access. Always ensure you get your Tor browser or any other software directly from verified sources only, not from third-party sites. Not just Tor alone, there are official sites for downloading every similar web browser APK. To provide anonymity, Tor is generally quite effective, but not completely foolproof. But using these tools for illegal purposes constitutes a criminal act either way.
How To Use The Tor Browser On MacOS And Windows
This segmented design makes it extremely difficult for any observer, whether it’s a website, ISP, or malicious actor, to trace your traffic back to you. The Tor Browser works by routing internet traffic through a global network of server nodes to mask your IP address and activity. While Tor offers strong privacy protections, it comes with notable drawbacks that can make it impractical for everyday use, and the dark web content it grants access to can put users at risk. That’s why savvy Tor users go a step further, encrypting all their internet data via a VPN first — a set-up known as “Tor over VPN” — adding a powerful extra layer of privacy that masks both your IP and Tor usage.
Despite the anonymity features of Tor Browser, users should also be aware of the potential for surveillance and tracking. While Tor Browser provides a degree of anonymity, accessing the dark web inherently involves exposure to a multitude of potential dangers. Unknown or suspicious links should be avoided as they may lead to harmful content, phishing sites, or malware. As discussed earlier, configuring Tor Browser’s security level is paramount for safer browsing on the dark web. While Tor itself encrypts traffic within its network, the connection between the user’s device and the first Tor node (the entry node) is visible to the ISP.
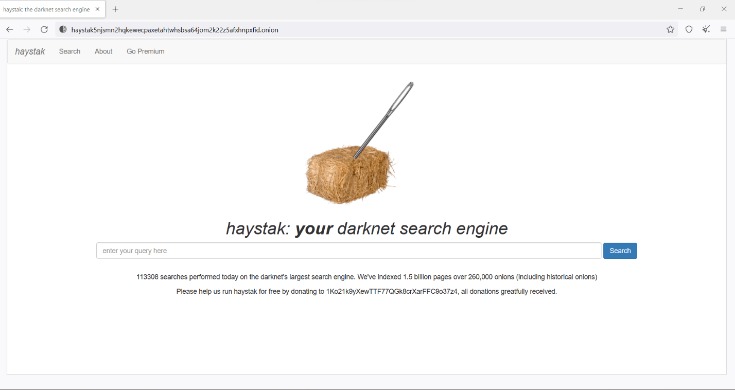
Yes, the dark web has a dark side, too — such as drugs, stolen data, and all sorts of illegal markets — but that does not mean that it’s just a home for criminals. The web uses onion routing, which caches your data through multiple layers of encryption over multiple networks. You can use search engines like DuckDuckGo or Torch to find the websites you want. Dark web websites have URLs that end in .onion, which usually consist of a 32-characters sequence of random letters and numbers. You will have to use specialized dark web search engines to find .onion sites. The process of onion routing takes your traffic, encrypts it, and bounces it among at least three relay points (or nodes), which makes it almost impossible to trace the source of the data.
- According to recent research, Bitcoin tumblers are increasingly used for money laundering.
- We highly recommend employing another layer of security via a VPN.
- The entry node is the first server in the Tor chain, the relay node is the middle node and the exit node is the last server in the network.
- The clear web is made up of websites that you can get to via a search engine like Ecosia or Google.
- Always ensure you get your Tor browser or any other software directly from verified sources only, not from third-party sites.
Built with multiple layers of security and Tor integration, it provides a robust environment to prevent malware attacks and safeguard user data. Subgraph OS is a Linux-based operating system designed for security, privacy, and dark web access. Whonix is a privacy-focused browser that operates in a virtual machine environment, creating a highly secure browsing experience on the dark web.

Never Download Files
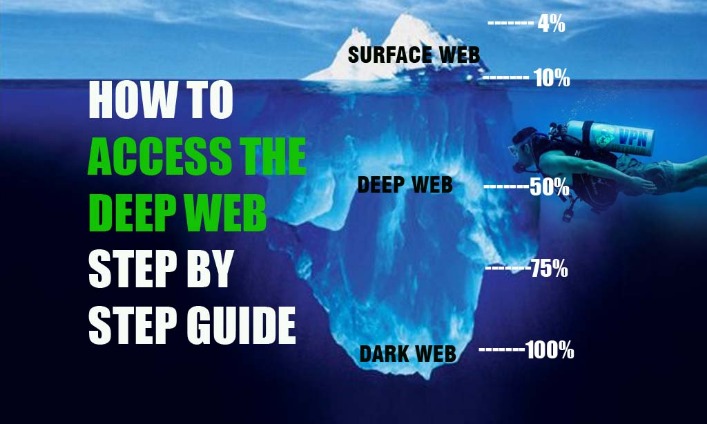
But, how can you get access to all these websites, pages, and information on the deep web and dark web if they can’t be found through Google, Bing, or Yahoo? All the websites and content that isn’t being shown on the “surface web” is generally referred to by many as the “deep web”, “dark web”, or “invisible web.” As well as attracting cybercriminals who use the anonymity it provides to offer hacking and phishing services, the dark web is awash with illicit forums, malware, and other potentially dangerous content. Without a VPN, your ISP or network administrator may be able to detect, monitor, or block dark web access; Tor-over-VPN provides an extra layer of privacy.
Additional Security Measures
It hosts encrypted websites, often used for privacy, anonymity, or illicit activities. The surface web is the open part of the internet, which includes publicly accessible websites and resources. Understanding how to access the dark web is valuable for IT leaders, cybersecurity experts, and professionals who need to monitor hidden threats or preserve online privacy. From cybersecurity researchers to IT managers, understanding how to navigate the dark web can help monitor cyber threats, protect sensitive data, and investigate cybersecurity incidents. Some governments actively monitor or block Tor traffic, and Tor use can raise suspicion even when not used for illegal activities. In rare cases, attackers can exploit an unsecure node to monitor Tor users or gain unauthorized access to accounts.
Blockchain analysis has become increasingly important in tracking cryptocurrency transactions linked to criminal activities. This topic is significant as it touches on privacy rights, cybersecurity concerns, and legal boundaries in an increasingly digital world. Explore the legal nuances of accessing the dark web, including potential penalties and jurisdictional differences. We're a nonprofit organization and rely on supporters like you to help us keep Tor robust and secure for millions of people worldwide. Tor Browser already comes with HTTPS-Only mode, NoScript, and other patches to protect your privacy and security.
Are Dark Websites Illegal To Use And Visit?
If you live in the EU and want to know what data your provider has collected about you, the GDPR gives you the right to request a full report. Furthermore, end-to-end encryption—like the kind securing your WhatsApp messages—makes that data unreadable to your ISP in the first place. In most regions, laws prohibit your Internet Provider from selling your data to third parties. If that happens, you can guess what happens to your data then. During that period, on top of the risk of accidental disclosure and theft, governments and the police could ask ISPs to share data.
Understanding Non-Human Identities In Cybersecurity How To Secure Ma
Even in an era of increased online surveillance, the average person on the internet likely has too much to lose to bet on their safety for curiosity's sake. Darknet browsers provide access to the dark web and allow for anonymous browsing. Users need to be cautious about the websites they visit and the files they download. By hiding IP addresses and sending traffic through encrypted tunnels, darknet browsers like Tor offer a high level of anonymity. On the other hand, it is illegal to use the dark web for criminal purposes or to obtain illegal content.
Don’t Download Files Or Click Ads
When using a dark web search engine, remember to exercise caution and verify the legitimacy of the websites you visit, as not all content on the dark web is safe or legal. Dark web search engines like DuckDuckGo can help you find specific websites or content within the dark web. By downloading and installing the Tor browser, you can access dark web websites securely. This specialized browser routes your internet traffic through a network of servers, concealing your IP address and encrypting your data. "All of your traffic goes through it, and you have to trust them as if they are your new ISP. Because the backbone of our software is a decentralised network, you don’t have to trust us to browse the internet privately." If you use the Tor browser to access a standard website, it offers protection and anonymity to users — they pop into the Tor cloud, that "onion space", and pop back out virtually elsewhere, with their identity and location obscured.
It is possible for personal information to end up on the dark web if it is obtained through data breaches or leaked from insecure sources. However, engaging in illegal activities on the dark web, such as purchasing illegal substances or participating in cybercrimes, is against the law and subject to legal consequences. In essence, managing personal information safely entails adopting a vigilant approach to safeguard privacy and security in an environment where anonymity reigns supreme but caution remains paramount. By dissociating online personas from actual identities, individuals create a necessary buffer between their private lives and their digital undertakings within this murky realm.
We’ll navigate this intricate maze with you, uncovering its secrets while ensuring your online safety. Our rigorous research and testing have revealed revealing truths and busted myths. It’s designed as an environment to elude detection, where site owners and visitors hide their identities. But lurking beneath lies the expansive, mysterious “deep web” or“dark net” – the gigantic submerged part that remains invisible to standard searches. On the internet, Google’s reach barely scratches the surface.
Your ISP may contact a government agency, like the FBI or NSA, who are always interested in suspicious online activity. That could make them suspicious about what you’re doing. Another reason you don’t want to use the Tor Browser for your daily web browsing is that it draws attention to you. Since your traffic goes through a series of relays, getting encrypted or decrypted along the way, things slow way down.
This includes resources requiring specific credentials or access, such as online banking portals, private databases, and academic journals. The Tor Browser stands as a specialized tool in the realm of internet navigation, designed to grant users enhanced privacy and anonymity while online. While services like Ahmia.fi can index certain 'onion' websites helping you remain safe, the same is not true for many other hidden services.