If you’re lucky enough, you can find it on clearnet privacy forums. If you want to find its current links, you can search for terms like “Daniel replacement.” Though it’s still helpful, a static list isn’t enough (we try to keep our own, the one above, up-to-date, though). Hence, you never know when a popular .onion site is going to vanish, or even die. These platforms keep changing their addresses to avoid DDoS attacks or law enforcement agencies.
Subscribe To A Formidable VPN
- So, if you’re looking for obscure Internet facts, very old documents, Berners-Lee’s brainchild is the way to go.
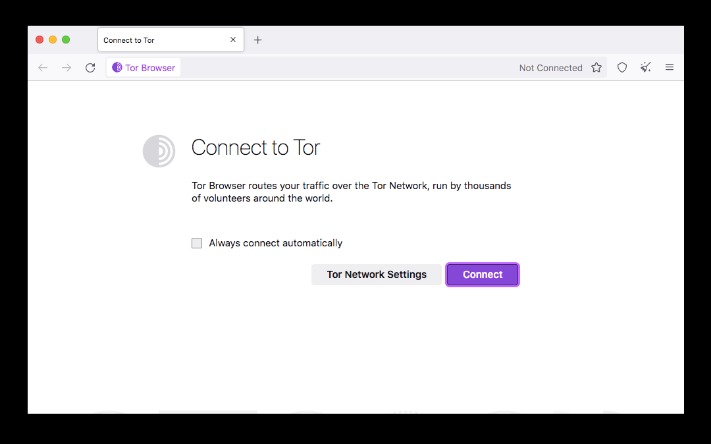
- Download Tor Browser to experience real private browsing without tracking, surveillance, or censorship.
- What gets you arrested is what you do once you’re there.
- The social media giant is also aware of the many attempts by repressive regimes to restrict its access.
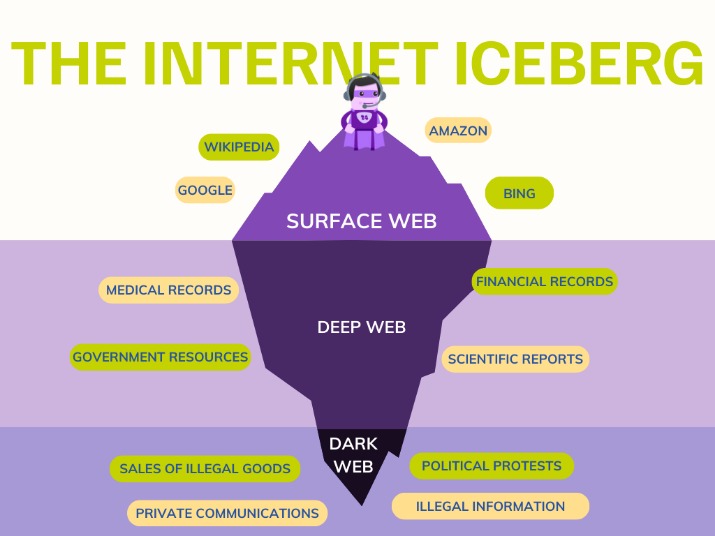
- Unlike the surface web, which we access daily through browsers like Chrome and Firefox, the dark web requires specific browsers to maintain user anonymity and ensure secure access.
These high levels of anonymity increase the opportunity for the “bad guys” to sell drugs, stolen IDs, credit cards, weapons, and many more compromised products or information. It’s no secret that the dark web can be a tricky and dangerous place for the general internet user. Simply download the file, install the software, and you’re ready to use its web-based interface.
A VPN app opens another potential vulnerability, as it can log the sites you visit via Tor. A common inquiry from Tor users is if they should use a VPN to add an extra layer of protection. It encrypts data during transmission to avoid the risk of being eavesdropped. It's what enables web browsers and servers to share information, including web pages and media files. Tor doesn’t support plugins because they introduce security risks.
MANAGED SERVICES
It is a complete operating system dedicated to advanced security and anonymity. It is a mobile application that uses your Android or iOS device’s VPN mode to route all traffic through the Tor network. A regular dark web browser will only encrypt your browser traffic; Orbot goes further and encrypts all data in and out of your phone.
The spy agency is hoping to securely and anonymously collect tips, though its entire website, including job listings, are available on the onion service. Indeed, Facebook, The New York Times and now even the CIA have sites on the dark web, hosting "onion" versions of their pages that can be accessed via the Tor browser. For more advanced use, Hyphanet allows you to create and host your own freesites, participate in forums, and communicate anonymously with other users. It’s designed for secure, decentralized storage and is often used for file sharing and accessing information anonymously. While Tor is the most common method for accessing the dark web, I2P and Hyphanet offer alternative options for secure and private browsing.
Do You Need A VPN If You Use Tor?
Whether you're a journalist, a privacy advocate, or just curious, this guide will walk you through how to access the dark web safely and responsibly. Some do, like Ahmia; others like Torch index nearly everything, including illicit content. The dark web is estimated to be significantly larger than the surface web, but much of it remains hidden or inaccessible. Search engines only index publicly known .onion links. No, many dark web sites are hidden or require invites.
Tor is a network designed to route traffic through multiple servers. It contains information like government private data, bank data, private networks, net-banking passwords, medical records, research papers, etc. Specialized deep web browsers are required to access the deep web as the normal search engines and browsers cannot be used to access it.

Are There Alternatives To Tor Browser For Dark Web Access?
And at the exit node, your decrypted traffic is vulnerable to interception. Anyone who owns and operates the entry node will see your real IP address. Plus, Tor cannot protect against tracking at the entry and exit nodes of its network. Tor Browser is primarily used as a method of anonymous browsing. Though Tor is slower, the process of rerouting data through nodes makes it more difficult to trace your activity back to you. In addition, Tor and VPNs take different approaches to rerouting data.
Accessing The Dark Web Without Tor: Setting Up I2P And Hyphanet
Living in a world where surveillance takes place, where you face constant threats almost daily, and where censorship reigns supreme requires tools to reclaim your privacy and security. Antidetect browsers are powerful tools that let you mask your digital fingerprints and manage multip… The Tor browser offers strong online protection, given that it routes your online traffic via severa…
MULTI-LAYERED ENCRYPTION
Tor traffic is decrypted at the exit node, which opens a vulnerability for malicious actors to inject malware or intercept traffic. Likewise, some websites allow Tor, but with frequent Captchas that can be annoying. You can also use it if you don’t want your network administrator or ISP to be aware of your Tor usage. You can use a VPN if you’re in a country that restricts or heavily monitors Tor usage.
Disadvantages Of The Tor Browser
The dark web is a segment of the deep web that is intentionally concealed and requires specific tools for access. Beneath the surface lies the deep web, a realm of unindexed content, and within it, the dark web. Using the Dark Web Browser can help maintain your anonymity for sure. Thus, it is one of the best-trusted browsers for anonymously exploring the web. Yes, you can access the browser directly from a USB or DVD. Similar to the Subgraph OS, the Tails browser is also based on the Tor network.

That said, the Tor browser also has some security issues, so it can’t 100% protect users’ privacy. It also provides some level of privacy and might allow people in restrictive countries to access the free internet. Avoid revealing personal details, exercise caution on shady websites, and always keep Tor Browser updated. It significantly reduces the ability of websites and trackers to identify you. By following these guidelines, you can explore the power of privacy while browsing online.
Broadly speaking, any internet browser can access the dark web with a few modifications. You can't open onion links via I2P, and you can't open I2P links over a Tor network. This traffic is transmitted in a single direction through the network, making tracking almost impossible. The Tor Project also offers the Tails operating system for users who prefer a complete privacy solution for accessing the dark web safely. When you use the Tor Browser, all your traffic will automatically travel through the Tor network, which comprises thousands of volunteer-run relays. It is the flagship product of the Tor Project (the company responsible for maintaining the Tor network).