Each of these nodes removes or “peels” away a single layer, which uncovers the data’s next node destination. The Tor Browser is configured to make all users look the same, making it nearly impossible for users to be fingerprinted based on their browser and device information. The browser uses a unique security system, which the United States Navy originally developed to protect the government’s intelligence communications. Suffice it to say that your Internet Service Provider (ISP) can detect when you’re using the Tor Browser, which can make you the target of increased surveillance by both the ISP and the government. Other users appreciate the browser as it allows them to circumvent censorship.

How To Access The Dark Web Safely: A 2025 Beginner’s Guide
The downside is that some websites block Tor connections by detecting its exit node. Outside or inside Tor, your traffic is secured 100% of the time. For one, the VPN can’t see your online activities because of VPN encryption.
Real-Life Example Of Attack Using Tor
The VPN will protect your traffic when you connect with military-grade AES 256-bit encryption. All the plans come with a 30-day money-back guarantee, so you can try the services risk-free. Since Tor has to pass your traffic through several nodes, it will slightly slow your speeds. In addition, it has an automatic kill switch (Network Lock) that stops traffic if the VPN connection fails. It offers multiple security protocols, including OpenVPN UDP/TCP, L2TP/IPSec, and PPTP. This will help you to remain anonymous and secure at all Tor entry and exit nodes.
Only Use HTTPS Sites
Furthermore, end-to-end encryption—like the kind securing your WhatsApp messages—makes that data unreadable to your ISP in the first place. In most regions, laws prohibit your Internet Provider from selling your data to third parties. If that happens, you can guess what happens to your data then. During that period, on top of the risk of accidental disclosure and theft, governments and the police could ask ISPs to share data. These laws mark how long ISPs must save the data they collect.
Given the dark web and the dark net’s anonymity principle, individuals can express themselves on unpopular issues but within the law. The dark web is designed to protect private information, keeping sensitive data out of the public eye. Talking about the fundamentals, the dark web and the darknet guarantee privacy and anonymity.
BBC Tor Mirror
- Understanding how to access the dark web is valuable for IT leaders, cybersecurity experts, and professionals who need to monitor hidden threats or preserve online privacy.
- Users should be well aware of these risks before venturing into this part of the internet.
- It is time for you to open your dark web browser, Tor, connect, and start browsing.
- Dark web sites are so well-hidden they can’t be accessed with normal browsers such as Chrome, Firefox or Safari.
A VPN combined with Tor provides better anonymity. Tor Browser masks your IP address and routes traffic through multiple servers. In this guide, we’ll cover the dark web access guide, explain how to use Tor browser safely, and answer key questions like is it safe to browse the dark web.
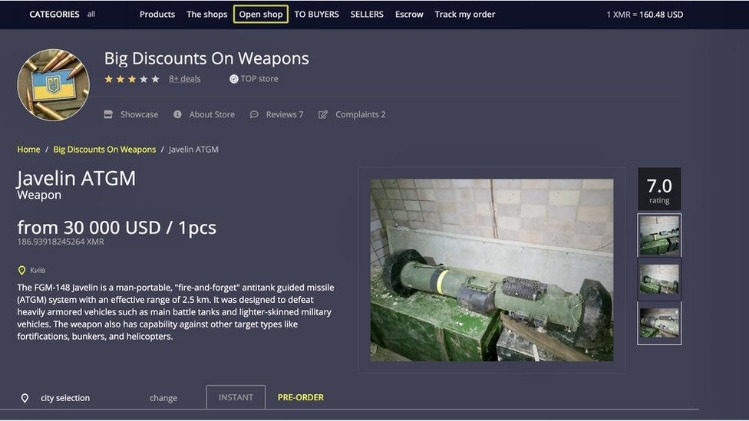
The dark web often connotes illicit activities like illegal drug sales and hacking. Yes, many organizations monitor the dark web for cybersecurity intelligence—always in line with legal compliance. The dark web refers to parts of the internet that aren’t indexed by standard search engines like Google or Bing.
I2P: The Invisible Internet Project
- Always double-check and cross verify before you visit an onion link.
- This is one last important security check to perform.
- Using advanced techniques, these agencies can de-anonymize users, especially those engaging in illegal activities.
- While Tor Browser provides a degree of anonymity, accessing the dark web inherently involves exposure to a multitude of potential dangers.
Relays help route traffic securely by passing encrypted data through multiple nodes before reaching its destination. They can monitor exit nodes but cannot easily trace traffic back to individual users unless mistakes are made. The Hidden Wiki is a popular onion link directory on the dark web offering categorized lists of sites. Yes, but for .onion sites, you’ll need search engines designed for the dark web like DuckDuckGo’s .onion version. The deep web includes non-indexed databases and private portals, while the dark web specifically requires Tor and includes .onion sites. Onion links are URLs that end with .onion and can only be accessed through the Tor network.
Is It Legal To Access The Deep Web?
We don’t slander highways or the internet, because that would be foolish. The freedom to communicate, publish, and read anonymously is a prerequisite for freedom of expression online, and thus a prerequisite for democracy today. In some countries, however, Tor is either illegal or blocked by national authorities. Tor does not support UDP, so don’t try to torrent free software ISOs, as it won’t work. Unlike Tor’s entry and exit nodes, bridge IP addresses are not publicly listed, making it difficult for web services, or governments, to blacklist those IP addresses. If you live in a regime that blocks Tor or need to access a web service that blocks Tor, you can also configure Tor Browser to use bridges.

Unknown or suspicious links should be avoided as they may lead to harmful content, phishing sites, or malware. As discussed earlier, configuring Tor Browser’s security level is paramount for safer browsing on the dark web. While Tor itself encrypts traffic within its network, the connection between the user’s device and the first Tor node (the entry node) is visible to the ISP. To mitigate these dangers, users should adopt several essential precautions before and during their browsing sessions.
Guide To Accessing Tor Via Tails OS On A USB Thumb Drive:
However, it’s crucial to exercise extreme caution when using such directories, as they can often contain links to unreliable, dangerous, or even illegal content, and the lists themselves may not always be up-to-date or vetted. As a result, users often rely on specialized search engines specifically designed to discover onion services. Unlike the surface web, where search engines like Google and Bing index vast amounts of content, onion services are generally not indexed by traditional search engines. These services utilize unique web addresses ending with the .onion top-level domain, signifying that they are accessible only through the Tor network. While this may cause some websites to lose certain functionalities, the enhanced security is often considered a worthwhile trade-off, especially when navigating potentially risky parts of the internet.
As a result, we deliver clear, actionable, and contextualized alerts, so your security team knows exactly what’s happening and how to respond—without wasting time. That’s why at TecnetOne, we don’t just collect data—we use smart technology and expert analysts to separate what matters from what doesn’t. We all know DuckDuckGo for its private search engine—but what you may not know is that it now has its own web browser, available on both desktop and mobile devices.