To cover themselves legally, their bio claims that all shared content comes from open sources on the internet, and that their purpose is educational. What makes MegaMedusa noteworthy is that it enables large-scale attacks without requiring advanced technical skills, making it accessible to anyone with malicious intent. They have gained notoriety for their DDoS attack campaigns targeting Ukraine, NATO countries, and allies of the Ukrainian government. This poses a serious risk to both individuals and organizations, as such credentials can be used in account takeovers, financial fraud, and unauthorized system access. In their bio, they describe themselves as “the largest and most versatile cloud on Telegram”, where logs extracted from other cybercrime channels are posted for easy access. With over 20,000 members, this community shares compromised databases containing usernames, passwords, email addresses, IP addresses, and more.
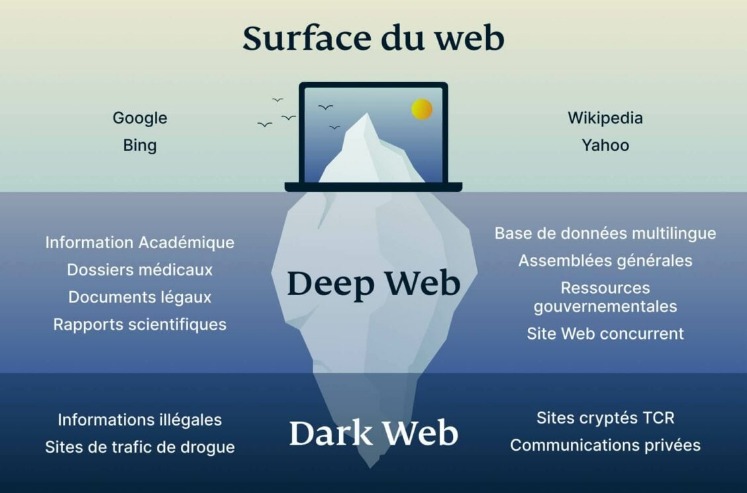
The dark web is the unregulated part of the deep web, which encompasses all parts of the web not indexed by search engines. Though not specifically a .onion service, Keybase integrates well with privacy-focused ecosystems like Tor. This platform allows visitors to anonymously explore the World Factbook, submit information, apply for jobs, and perform any other actions available on the CIA’s main site.
Tor And The Onion Browser
This forum utilizes the military-grade symmetric cipher AES 256 CTR for encrypting messages. This dark web forum was initially leaked in 2020 and caters to the cybercriminal and hacker elites. This is because much of the dark web is still prominently full of threat actors eager and willing to connect with others to commit the latest hacks or attack methods successfully. The dark web is commonly a place where individuals can operate under the guise of anonymity. This is because it is a non-public facing corner of the internet that isn’t visible to search engines and requires special browsing capabilities. Often misrepresented as accessible from the greater public view of the internet, the dark web is actually not as readily as accessible as it may seem to be.
What To Do If You See Something Illegal
Nevertheless, the digital landscape is under constant cyber threat, and individual or business data can find its way onto the dark web. Perhaps the strategy should include a remediation process when exploits are detected during the monitoring. Dark web monitoring is done with the aim of high ethics as well as intelligence gathering. Our article here lists good options if you want to explore such tools. Therefore, there are various best practices that an organization can follow to ensure that it strengthens the overall monitoring efforts.
- In the same way, the administrators of darknet markets don’t directly sell illegal drugs and malware, they provide the platform.
- Card data is a hot commodity on the dark web, with credit card details and cloned cards being sold to cybercriminals.
- These categories include sections for cracking, hacking tutorials, coding, leaks, and marketplaces.
- With this in mind, finding verified links is crucial for avoiding threats on the dark web.
- It is also used by whistle-blowers, journalists, and other individuals who are not involved in illegal activity but need to protect their communications and identities.
Credit Card Fraud On The Dark Web
And there is no connection between the corporation which owns Reddit and the administrators of Dread. Most subs never become popular, but a handful can have millions of active users. I enjoy doing cyber threat intel research there, I learn more and more everyday. The darknet is simply a part of the internet which is only accessible through encrypted proxy networks, namely Tor and I2P. Not all activity on the Dark Web or “darknet” is illegal. Of the Italian cards, roughly 50% have already been blocked due to the issuing banks having detected fraudulent activity, which means that the actually usable entries in the leaked collection may be as low as 10%.
In 2018, the founder was caught and the first forum was closed. Founded in 2008, Altenen has 1.3 million users and 1,264,546 posts. When writing this report, the XSS forum has 81,002 threads, 625,178 messages, and 58,902 members. Again, like the Breach forum, XSS offers free user account creation. The forum contains a significant amount of exploits, zero-day exploits, and malware. XSS, a Russian forum, has been actively used for cyber attacks since about 2013.
"Does The Dark Web Have Forums?"
For example, a known Telegram channel in the hacking community operated by the name BF Repo V3 Files that constantly stores and shares backup files from data breaches, if talking about leaked passwords, combos (including email addresses), KYC, ID screenshots, or even full documents belonging to a country or a company. Since Telegram is one of the most popular chat applications among cybercriminals, we’ll take a closer look at examples we found by using our Cyber API that show how threat actors use both dark web sites and Telegram for their illegal operations. It is worth noting that we have seen a drastic increase in the usage of IM apps over traditional dark web sites and marketplaces, especially Telegram black markets.Due to the advantages and the ease of use of those apps, even to a level where some known forums now operate only on Telegram and ditched the dark web completely. Operating since 2020, 2easy Market is a dark web marketplace known primarily for its focus on stolen data and cybercrime services, particularly targeting compromised accounts and personal information. The market frequently makes headlines for releasing massive troves of stolen data, often as a way to advertise its services.
Founded by security researcher Juha Nurmi, Ahmia is essentially a list of “hidden” sites that do want to be found. Needless to say, it takes your data much longer to travel this way, which means dark web links load slowly compared to indexed sites. Onion sites (aka Tor sites) are websites only accessible on the dark web; you can’t view them using a regular browser. Scroll on to learn more about dark web links (also called Tor links or onion sites), get the right links for some of the best Tor sites, and find out how to visit them safely.
Live Credit Cards
As of 2020, nearly 57% of the dark web was estimated to contain illegal content, including violence and extremist platforms. These platforms sell everything from drugs and fake IDs to weapons and hacking tools, resembling a digital black-market bazaar. Despite growing crackdowns from law enforcement agencies, the dark web remains a hotbed of criminal activity, offering everything from drugs to stolen data.

One compromised payment processor or e-commerce platform can yield thousands of card numbers at once. They’ve essentially created a parallel economy with its own reputation systems, escrow services, and even customer support channels. The pricing varies based on the card type, with premium cards from certain banks fetching higher prices. Credit card fraud on the dark web operates quite differently from what many people imagine. But first, how big of a problem is credit card fraud on the dark web? Dark Web credit card fraud is an ongoing problem and is not showing any signs of going away.

Best Dark Web Sites: Unseen Onion And Tor Links
The process costs a fee, but unlike other "tumbler" or "mixing" services, there is no risk that Wasabi or any of its users could scam you out of your coins. Wasabi Wallet is a Bitcoin wallet that not only hides all your data in the Tor network but also allows you to "join" your transactions with others to increase your anonymity. In that spirit, the CIA launched an onion site to help people around the world access its resources securely.
Online Shopping Without CVV Code: The Real No-Front Street Guide
The resulting financial loss from stolen information is tremendous, not only for the individual victim but also for the financial provider and any involved organizations. Such type of data is likely to have been compromised online, making it a red flag for would-be fraudsters. A recent arrest in the Southeast Asia region marked the first time JS-sniffer operators have been caught anywhere in the world. The cards were likely compromised online, using phishing, malware, or JavaScript-sniffers, which are increasingly popular among cybercriminals. This dataset is more valuable than the previous one, as it includes CVV/CVC codes and other sensitive information.
While stealing card data can sometimes be relatively easy, successfully using it is far more difficult. There’s a wealth of information shared among carders—from how to bypass anti-fraud systems to practical guides on using stolen credit cards—all of which helps keep the ecosystem active and evolving. Marketing around carding is designed to make it feel easy and accessible—even for newcomers.
- Stay private with a tool like Surfshark’s Alternative ID to mask your contact details and use generated data on sites you don’t trust.
- Because of its anonymity, the dark web is filled with illegal services and is used by numerous criminal groups, including ransomware gangs.
- The analysts claim these cards mainly come from web skimmers, which are malicious scripts injected into checkout pages of hacked e-commerce sites that steal submitted credit card and customer information.
- Dread’s strength lies in its decentralized community structure, solid moderation, and security measures that help it withstand DDoS attacks.
- Note that some features of the normal website are not available on the .onion version, including BBC iPlayer.
No matter what you’re looking for on the dark web, it's crucial that you safeguard yourself with the highest level of privacy and security. But unless you’re an expert dark web navigator, we advise using extreme caution when using either one. The deep web consists of all parts of the web that aren’t indexed by standard search engines like Google. A common misconception about the dark web is that it’s the same as the deep web, but this is not the case. Unlike many search engines that avoid the darkest corners of the web, Kilos actively delves into these areas without filtering search results.
Why Do People Visit Dark Web Forums?
That is why in 2006 they created "the most private search engine in the world", which does not record, track, or share your personal data. This virtual bookstore is one of the oldest search engines on the internet. Tor Search is a very efficient search engine because it indexes new content all day from the TOR network. At the moment they are making minor improvements to the search engine and working on the Beta version of their new link directory.