As a result, you should avoid opening unfiltered sources, torrent sites, and dark web links unnecessarily and downloading every file you come across. Many dark net sites do not undertake the necessary measures to protect users like most websites on the surface web. With rising online privacy concerns in the current digital age, the Tor network’s anonymity is becoming essential. For example, it maintains your privacy and enables you to access untraceable content and services. Other sites explicitly block search engines from identifying them.
- As a result, it is probably a good idea to double-check and verify any onion links you find using a secondary source such as Onion Links or DarkWebPug.
- Back when reliable dark web search engines were limited, the Hidden Wiki served as a trusted compass for exploring the hidden layers of the internet.
- Only about 7.5% of the child sex abuse material on the Tor network is estimated to be sold for a profit.
- Its goal is to offer anonymous access to the content without being censored, no matter where you live.
SecMail is one of the most popular email services on the dark web. Even without the code, you can visit the security section to get tips on improving your daily life privacy. In addition, it ensures that no record of communication is stored. It was created in 1999 as a secure communication platform for people and groups working on liberatory social change. RiseUp is a top dark web website that offers secure email services and a chat option.
Access The Dark Web Anonymously & Securely
This process also prevents your ISP from seeing your data or where it’s going. Your ISP, and possibly the authorities, may decide to start monitoring your activity more closely to look for threats or illegal activity. While people and organizations do host legitimate and useful sites on the dark web, it’s still best to tread cautiously. With that said, legitimate websites also exist on the dark web. Through the dark web, users in places of high censorship can also access information and news. While technically not an onion site, we’re including Sci-Hub (sci-hub.se) as an interesting example of a site you can access via Tor.
Defend Yourself Against Tracking And Surveillance Circumvent Censorship
A recent effort led by German police, and involving others including Australian Federal Police, Europol and the FBI, resulted in the shutdown of the illegal website Boystown in May. Only about 7.5% of the child sex abuse material on the Tor network is estimated to be sold for a profit. Among the visited services, child sex abuse material is common. The Tor Project was initially developed by the US Navy to protect online intelligence communications, before its code was publicly released in 2002. The latest rumblings from the EU tech scene, a story from our wise ol' founder Boris, and some questionable AI art. Child sexual abuse material is rampant online, despite considerable efforts by big tech companies and governments to curb it.
BBC News /nepali नेपाली
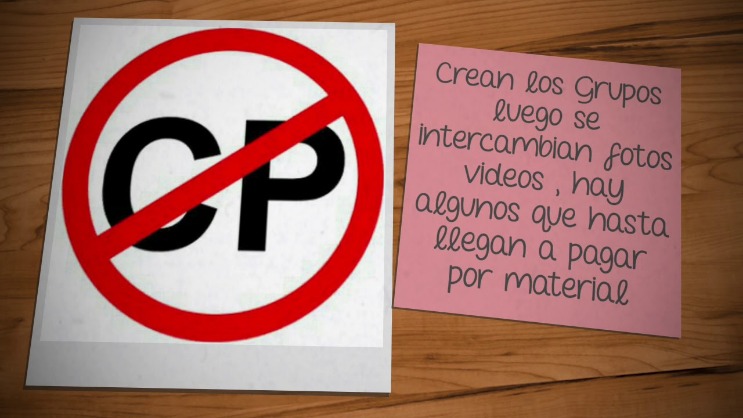
Little is known about child sex abuse material forums on Tor, or the extent to which they influence onion services hosting this material. One example is targeted “hacks” which offer law enforcement back-door access to sites or forums hosting child sex abuse material. That said, some services have started charging fees for content. It enables users to browse the internet anonymously by hiding their identity and location. Tor is an overlay network that exists “on top” of the internet and merges two technologies.
Illegal Markets
Onion sites aren’t really dangerous, but they could be when accessed through unfamiliar or suspicious links. It has a proprietary onion site in the Tor network to give you safe access even if your country restricts VPN usage. This means you will get a VPN’s security and enjoy the anonymity of the Tor network simultaneously. The Tor browser allows you to browse the internet anonymously and visit inaccessible sites.
We find the age information in total for 479,555 search sessions. We determine if the search session reveals the exact age in which the CSAM user is interested. Surprisingly, we find that before and after COVID-19 pandemic measures (lockdowns, individuals spending more time at home), there were no significant changes in the behaviour of CSAM users (see more in Supplementary Methods A.8). (c) We execute text-based CSAM detections against the content of these distinct domains.
RESOURCES
When a website has multiple alternate onion domains, we eliminate duplicates. Websites that share CSAM make this fact abundantly evident on the front page (see Supplementary Methods A.3), as well as through the use of explicit, distinct wording. To extract only the textual content, we use the html2text Python library to convert the HTML pages to plain text representation. We investigate the years 2018–2023 and use a random sample of 10,000 unique onion domains for each year. We ask CSAM users about their thoughts, feelings, and actions related to their use of CSAM so that in the future we can build a cognitive behavioural theory-based anonymous rehabilitation programme for CSAM users.
Using Tor Browser FAQs
Tl;dr – HTTP-over-Onion should not be considered as secure asHTTPS-over-Onion, and attempting to force it thusly will create afuture compatibility mess for the ecosystem of onion-capable browsers. You can also see the history of updates. These sites have apparently stopped responding. Provides shared notepad, spreadsheet, pastebin, and other services Provides shared notepad, file sharing, code hosting, and other services
Dark Web Links For News
It’s an easy and simple way to de-couple your internet usage from Google’s monopoly over the web. SimplyTranslate is an onion based language translation service using the google translate engine. Pastebins are text sharing services, usually for sending and sharing text snippets. ZeroBin is another great Tor service that helps maintain anonymity and privacy by offering an encrypted pastebin service.
It is essentially a list of all the notable websites available on the Tor Network that is kept in a single, organized place. The Hidden Wiki is one of the easiest ways to find useful resources and websites on the Dark Web. Please note that you must take great care when using the Dark Web as sites often contain adware, spyware, malicious links, and scams. Tor works by directing internet traffic through a global network of volunteer nodes. The Dark Web may have a sordid reputation, but there’s plenty of legitimate websites out there for people who just want to browse anonymously. Well, as long as you don't visit sites with underaged models or that engage in human tracking or that sell drugs and other illegal items.
- The BBC and other well-known news services are blocked in some parts of the world.
- This search engine's mission is to be leaders in providing services on the deep web, protecting the anonymity of each user.
- Simply put, accessing and browsing the dark web is perfectly legal.
- A VPN connection is key to gaining greater privacy, security, and freedom on and off the dark web.

One option is to try DuckDuckGo’s .onion version, which is great for privacy. The best thing is to actually understand how to find the fresh, new links. Though it’s still helpful, a static list isn’t enough (we try to keep our own, the one above, up-to-date, though).