Within these closed ecosystems and forbidden Telegram channels, threat actors can coordinate and operate with little risk of detection. Additionally, the ability to create large, private groups and dark web telegram channels significantly compounds the challenge for cybersecurity teams. The ephemeral nature of some Telegram communications, such as self-destructing messages, adds another layer of complexity to threat intelligence efforts, requiring real-time monitoring and analysis to capture and preserve crucial information. This necessitates the development of advanced analytical techniques and tools to effectively monitor and analyze the vast amounts of data exchanged within these encrypted environments. In the wake of Edward Snowden’s revelations concerning government surveillance, Telegram was built in 2013 to prioritize user privacy and safeguard private conversations and data from third-party intrusion.
Community Forums
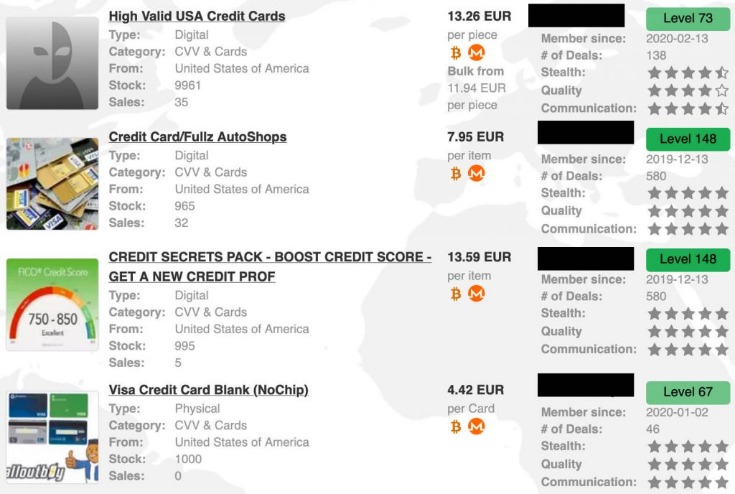
These cryptocurrencies offer additional layers of anonymity and privacy, making them attractive alternatives for certain transactions. Due to the anonymity provided by the Dark Web, traditional payment methods are often not acceptable. – Read feedback from experienced Dark Web users or trusted individuals who have had successful transactions with the vendor. – Take note of any patterns or recurring issues mentioned in the feedback, such as inconsistency in card quality or lack of response from the vendor. Vendors who offer encrypted messaging platforms or use PGP (Pretty Good Privacy) encryption indicate a commitment to their customers’ privacy and security.
Monitoring the dark web for your credit card number is crucial for anyone who wants to protect their financial security. Exposure of your credit card details can lead to fraudulent activity, which could negatively impact your credit score. In fact, the overwhelming majority of leaked credit cards in past months originate from Telegram channels. These platforms serve as hubs for cybercriminals to easily buy and sell compromised payment card details, including credit card numbers, CVV codes, expiry dates, and cardholder information.
Related Content
Scanning helps catch exposure early and prevents financial damage. The global average cost of a data breach Understand the real risks to your personal information. Use this guide to learn how to easily automate supply chain risk reports with Chat GPT and news data. Monitoring the deep and dark web becomes imperative for proactive defense against such threats.
Darkweb Market BidenCash Gives Away 12 Million Credit Cards For Free
Digital banking apps now have built-in fraud alerts. Multi-factor login adds extra security. This helps stop fraud before it starts. Detecting unwanted transactions is key to protecting your finances. This extra layer of security gives peace of mind in today’s digital world.
11 North America faces the biggest threat, with 42% of global e-commerce fraud value. Encryption keeps card info safer online. Next, we’ll look at how tech fights dark web card fraud.
This threat intelligence enabled several major FIs in the U.S. and abroad to detect similarities in account openings, transactions anomalies, and mailing addresses used by fraudsters. Resecurity identified multiple underground vendors providing cash-out services from stolen VCC, banking, e-commerce and cryptocurrency exchange accounts. Typically, the fraudsters use compromised or purchased access via a reputable credit bureau’s third party and exploit their services for illegal purposes. Besides payment data, threat actors are also monetizing stolen Personal Identifiable Information (PII).
Is Monitoring Dark Web Forums Important? Why?
- Clearly communicate your interest in purchasing the specific credit card details and any additional requirements or inquiries you may have.
- Dark web markets are like hidden online stores, except instead of selling clothes or technology, they specialize in illegal products and services.
- It re-emerged on June 12, 2023, under ShinyHunters, a notorious threat group.
- However, with the right approach and tools, individuals can discover these hidden marketplaces.
- A vast majority of bank and credit card apps offer notifications and alerts for questions about suspected fraud.
- In some cases, it’s also used for private messaging, cybersecurity training, whistleblowing, and other legitimate uses.
The site is accessible via both Tor and the clear web, and its layout closely resembles that of Abacus Market, which makes navigation very user-friendly.Notable features include an automated carding shop, an escrow system for manual orders, and a dashboard that displays balances in both BTC and Canadian dollars (CAD). There are RDP accesses, SMTP logins, SSH credentials, fake pages, and even fraud tutorials. If someone wants direct access to a server, a cPanel, or an email, this is the place to go.The market is in English and features a massive catalog with over 800,000 illegal products. Each of these “bots” represents a compromised device, and prices for access range from $3 to $10, depending on the quality and freshness of the data.However, it works by invitation only and is accessed through several mirrors on the Tor network. The truth is that, despite the incident, the site is still active and constantly renewing its inventory.Thanks to its track record, loyal user base, and continuous flow of updated data, BriansClub remains a key player in the current landscape of dark web fraud. Russian Market has been operating since 2019 and is one of the favorite destinations for those looking for stolen digital data, rather than physical products.
You Can Protect Your Business And Consumers From Darknet Data Leaks Contact Us To Discuss How
• 4.5 million credit card numbers were sold on the dark web in early 2022 Stolen credit card info sells fast on dark web markets. 2 Next, we’ll look at how credit card info ends up on the dark web. The dark web makes it easy to buy and sell stolen cards anonymously. Criminals steal card details and sell them online.
Start Your Protection,
Continue reading to learn how your credit card information could have gotten on the dark web and how to keep your credit card information safe in the future. I’ve seen cases where security teams identified compromised card data from their institution appearing on the dark web weeks before they traced the actual breach point. When we spot cards from these BIN ranges appearing in bulk listings, it often indicates a breach somewhere in the payment chain.
Finding Dark Web Marketplaces
Once an order is placed, the victim will receive multiple e-mail notifications primarily coming from third-party online services. According to the vendor’s service offering, HubExpert’s operators are continuously working to improve the fraud tool’s delivery mechanisms. In exploitation scenarios, this compliance unit may call a victim to confirm suspicious account activity or send a text message or email.
Stolen credit cards are used to cash them out or make purchases that can be resold. Dark web credit card numbers are stolen card details sold on hidden websites. Criminals use stolen credit card data to make fake purchases. Dark web transactions play a key role in fund transfers for credit card fraud. The vast majority of the stolen credit card records came from Indian banks UPDATED A database featuring more than 460,000 payment card records – almost all from India – is being offered for sale through a darknet bazaar, threat intel firm Group-IB warns.
One reputable STYX Marketplace vendor focused on stolen PII is the “Fraud Store”. In Q1 2023, Resecurity observed a significant spike in interest from bad actors seeking these tools, as well as the emergence of new fingerprint spoofing and anti-detect products on the Dark Web. One notable STYX Marketplace product is listed by “Enclave Service”, a reputable service on the Dark Web that provides tools for identity spoofing and anti-fraud bypass. Some of the service descriptions are limited – the marketplace connects actors via Telegram contacts and various automated bots as a security measure.
Depending on the goal of a cybercriminal, they may prompt you to enter your login credentials or your credit card information. A compromised online account is an account that has been accessed without the permission of the person who owns it. Here are the steps to take after discovering your credit card information is on the dark web.
- In Q1 2023, Resecurity observed a significant spike in interest from bad actors seeking these tools, as well as the emergence of new fingerprint spoofing and anti-detect products on the Dark Web.
- There are currently several online darknet markets, but they tend to be incredibly volatile due to government intervention.
- Cybercriminals can use this information to impersonate you, open fraudulent accounts under your name and make unauthorized transactions.
- Thieves often buy cards to use on specific sites that don't have security features like Verified by Visa (VBV) or MasterCard's SecureCode.
“It’s a kind of insurance that you will get the details of another stolen card instead, if the card you purchased is invalid.” This is because criminals can purchase cards to use in their own geographical locations to limit the chances that their transactions will be flagged. “Now, they sell individual cards for X amount of dollars, and you can go and very quickly make fraudulent purchases before the card is deactivated.” Mador says the criminals who purchase stolen cards have different goals in mind. The proceeds from sales of card numbers are used for enabling organized crime and gang activities, weapons exchange, trafficking drugs and guns, and many other illegal activities, he says. And if you can then have it come out the other side in the form of a credit card, then that’s generally accepted just about anywhere, from a mega-reseller to your mom-and-pop pizzeria.
How Does ThreatMon Monitor The Dark Forums?
The data includes the service code, PIN code, and card verification code, making it highly valuable for thieves. Credit card details can be sold as digital items on the dark web, with the basics costing around $17.36. Card data on the dark web is a valuable commodity, and it's often sold on specialized marketplaces known as Card Shops. This financial loss can occur through unauthorized charges, account takeover, and identity theft.
Illegal activities thrive on the dark web, including the illicit trade and sale of credit card information. To protect yourself, it's crucial to monitor your credit regularly, report any suspicious transactions promptly, and use secure payment methods online. Criminals exploit the anonymity and encryption features of the dark web to buy and sell stolen credit card information. Additionally, phishing scams and malware-infected websites are utilized to trick unsuspecting victims into providing their credit card details unknowingly.