
Consenting to these technologies will allow us to process data such as your IP address and browsing behavior or unique IDs on this site. Tools such as VPNs can make it somewhat safer to browse, but people should still exercise extreme caution whenever visiting web pages on the darknet. While it has legitimate uses, it’s also a hub for cybercriminals, hackers, and other threat actors.
Advanced Market Selection Strategies
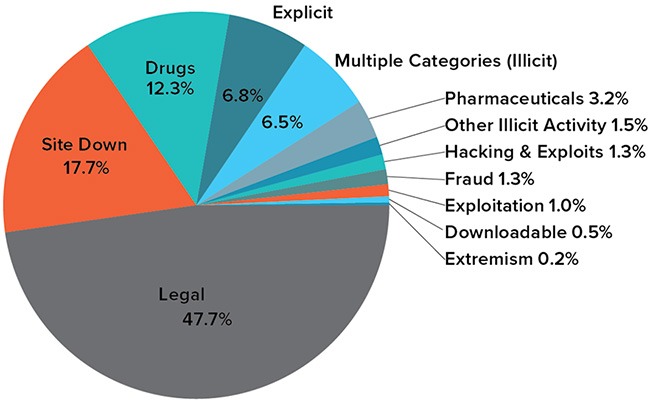
While anonymity tools make it hard, skilled investigators take advantage of mistakes and covert operations to break cases. Chainalysis estimates $ billion in crypto was moved through dark markets in 2022 drugs, data, and everything else combined. A recent report noted 92% of major marketplaces offer escrow and dispute resolution, mimicking legal e-commerce trust models. The core of daily dark web activity is marketplaces and forums.
While dark web search engines are essential for accessing the dark web and monitoring potential threats to your business, they also pose their own risks. While you can access it through Tor for privacy, it doesn’t index .onion websites. It offers an uncensored experience that does not log any personal data, making it a favorite for privacy-conscious users who want unbiased results. Its index is partially built on user-submitted .onion sites. This lack of filters means users are frequently exposed to harmful sites, spam, and abusive content. Ahmia is one of the better-known dark web search engines, indexing .onion sites on the Tor network.
- Tor adds a layer of anonymity, which helps dark websites remain hidden and prevents conventional search engines from indexing them.
- The evolution of darkweb markets can be traced back to the early 2000s with platforms like Silk Road, which revolutionized online trade and highlighted the potential of cryptocurrencies for anonymous transactions.
- OnionLinks is not a search engine but rather a categorized directory of .onion websites.
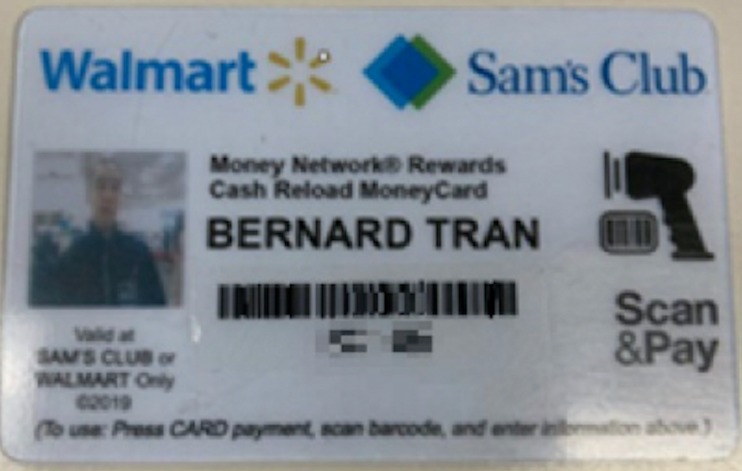
- Over the past decade, it has built a reputation as a reliable source for huge volumes of credit cards and personal data.
Ready To Explore Web Data At Scale?
However, darkweb market adaptation frequently outweighed these efforts, leading to the development of new platforms almost immediately following closures. Additionally, decentralized networks and new privacy tools strengthen darkweb market operational frameworks by enhancing their resilience to shutdown attempts and surveillance. Users and vendors alike are at risk from product closures caused by law enforcement actions or internal disputes, making the environment volatile. Despite these challenges, law enforcement continues to develop new methods to monitor and intervene in these illicit activities.
Challenges Facing Dark Web Intelligence Systems
Learn about the top markets, their features, and how they maintain privacy and safety in an ever-changing landscape Acting on a search warrant on their homes, authorities found millions of dollars in cash, drugs, and a variety of weapons. The investigators believe that the money held in escrow is approximately $11 million.
The vendor then lists their products or services on the market, and buyers can purchase them using cryptocurrency. To become a vendor on a darknet market, one typically needs to create an account and deposit cryptocurrency into it. Despite these efforts, the sheer volume of data breaches and the anonymity provided by the dark web make it a persistent challenge. Vendors often increase their market presence by listing products on multiple markets, which helps them maintain their reputation even if one market faces closure. Darkweb markets facilitate a wide array of transactions, with illicit drugs remaining the most traded commodity. It is a network of encrypted websites and servers that can only be accessed through specialized software, such as Tor.

Want To Browse Anonymously?
To maintain trust and protect users, they implement various measures. Current markets are always changing, and you can find a collection of working links here. Hydra, a behemoth with millions of users, offered a vast array of products, from everyday items to illicit goods.
Cyble Titan Endpoint Security
This unlisted, fragmented, and transient environment is a playground for cybercriminals—and these search engines are the most direct way to find them. These search engines are often the primary entry point to the internet's underbelly. Yet some of today’s biggest risks—such as data breaches, identity theft, and corporate espionage—often originate on the dark web. However, for business leaders and security professionals, ignoring this part of the web is no longer an option. It's a hidden layer of the internet beyond the reach of traditional search engines. Staying current requires continuous monitoring of the dark web ecosystem.
- Despite repeated law enforcement crackdowns, dark web marketplaces remain a thriving underground economy in 2025.
- Businesses can use deep and dark web monitoring tools to keep track of stolen credentials or mentions of their brand to protect against cyberattacks.
- Cops and bad actors are both getting smarter tech-wise.
- The dark web marketplace landscape in 2024 is a diverse ecosystem, each platform boasting unique features and catering to specific clienteles.
- Second, the dark market sites accepted payments for their illicit goods and services in Bitcoin or similar electronic currency designed to be as anonymous as cash.
- Like traditional search engines, dark web search engines also use web crawlers, though not the same ones.
Dark Web Marketplaces & Illicit Goods
Additionally, you should not share any information to any sites that might cause you to be identified or linked to your name or other identifying information. You will also want to use a VPN, which will add another layer of protection and anonymity. The Tor network itself was designed originally for secure communications by the government, and is used frequently by journalists, human rights activists, and privacy advocates. Your original IP address is passed through a series of encrypted nodes (or hops), ultimately hiding the user's identity (or IP). While the surface web gives the impression of privacy, the deep web has a stronger focus on privacy and, therefore, is an important tool for journalists, researchers, and privacy-centric individuals.
Server hardening involves securing operating systems, disabling unnecessary services, implementing firewalls, and regular security updates. However, backups also represent security risks if not properly encrypted and secured. Secure markets maintain encrypted backups in multiple locations, enabling rapid recovery. Sklad's decentralized architecture represents the future of darknet market design, providing unprecedented resilience against takedowns.
Which Top Companies Are The Leading Key Players In The Dark Web Intelligence Industry?
However, always follow best practices such as using a VPN and opting for privacy-focused cryptocurrencies like Monero for enhanced security. They also implement strong privacy protocols such as mandatory usage of Tor and, in some cases, multi-signature wallets. DrugHub Market stands out for its strong emphasis on privacy and security. Emerging at a time when the dark web was witnessing the shutdown of several major platforms, Anubis sought to fill the gap left by these closures. The platform uses encryption and secure communication protocols to ensure all transactions remain private and anonymous.
The forum hosts multiple sub-communities, where users discuss everything from data leaks to illegal drug sales. The forum specializes in a variety of illegal activities, including the sale of leaked data, hacking tools, and fraudulent services. While these databases are invaluable tools for cybersecurity experts, aiding in research and threat analysis, they are also used by cybercriminals to boost their activities and “brand”.
What The Future Holds For Dark Web Marketplaces
Avoid mentioning markets, vendors, or orders on social media, messaging apps, or email. Never use cryptocurrency purchased with personal information directly on darknet markets. Understanding and implementing proper OPSEC practices is essential for safe darknet marketplace usage. DDoS attacks represent constant threats to darknet markets.



