
If you make use of a password manager, then it may come with a feature that monitors the dark web for mentions of your email address and password, or any other personal details. (Presentation and polish isn't quite so important on this part of the internet.) Click on any website link, and it'll appear on screen, with its address at the top. Individual sites on the dark web look much like they do on the regular web, though a lot of them are a bit more rough around the edges. These typically come with ".onion" after them, rather than something like ".com" as on the standard web.
Use The Right Tools: Tor And Beyond
The Dark Web often carries a stigma, primarily due to its association with illegal activities. Instead, users must use specialized browsers designed to provide a high level of anonymity. The Dark Web is not something easily accessible, nor is it a place where casual users tend to wander.
Privacy Marketplaces
Its commitment to user privacy, combined with its comprehensive suite of tools, makes Tails an essential asset for Tor enthusiasts. Tails is a unique operating system tailored for those who prioritize privacy and security. With its focus on user privacy and a clean, user-friendly interface, Ahmia has become an indispensable tool for many Tor users.
The dark web and deep web are home to countless hidden forums where users discuss everything from privacy tools to cybersecurity to hacking,… Yes, there are search engines specifically for the dark web that index .onion sites. To access dark websites, you’ll need a dark web search engine like Ahmia or Torch. Most people rely on the Tor browser to access .onion links, which is relatively secure. While it’s not as big as regular clearnet search engines such as Google or Bing, Haystak has more than 1.5 billion pages and 260,000 onion URLs indexed. Interestingly, when Tor upgraded its network in 2020 (from V2 to V3), dark.fail was quick to adopt the new, more secure onion links.
It's a collection of websites and services that exist on an encrypted network, accessible only through special software like the Tor Browser. While these databases are invaluable tools for cybersecurity experts, aiding in research and threat analysis, they are also used by cybercriminals to boost their activities and “brand”. H25.io is a premium directory in the Tor network, offering access to a diverse and meticulously curated list of onion sites.
The Surface Web
It serves the same purpose as ProPublica – facilitating access in countries where it may otherwise be restricted. There’s a reason why this onion website is called the Imperial Library; with over downloadable 500,000 books and articles, this may be one of the largest digital libraries, period. I think it’s safe to say that these are unsanctioned exploits, all the more reason to boast them on the dark web. No info is available on the explored institutions or how these sections can be accessed. I have to admit to having a soft spot for Tunnels, an onion website about underground “urban” exploration. I can tell you what it’s not – a digestible dark web website.
It has been intentionally hidden and requires special tools, like the Tor browser, to access. The deep web refers to any part of the internet that is not indexed by search engines. The dark web is a part of the internet that isn’t indexed by search engines like Google or Bing. The “surface web,” on the other hand, is the publicly available part of the internet that search engines index.
This is so you can reliably conceal your IP address and encrypt your internet connection. Before you even think about connecting to the dark web, it’s crucial that you connect to a reliable and safe VPN. In other words, the dark web is not the entire deep web, it's not a physical location, it's not a single entity, and not all activity on the dark web is illegal. These connections are often used by organizations and individuals to communicate and share information in a secure and private way.
Monitor System Resources

Due to its dedication to accuracy and privacy, Haystak is a favorite among journalists, academics, and threat analysts searching the dark web. The tool is designed so that even the server cannot read the content you paste. It’s one of the few resources that consistently updates its .onion mirror, ensuring availability even during domain seizures or censorship events. The platform is open-source, audited, and designed to protect both the sender and recipient. Every installation has its .onion link hosted by the respective publication. While many users begin their dark web journey here, caution is strongly advised.
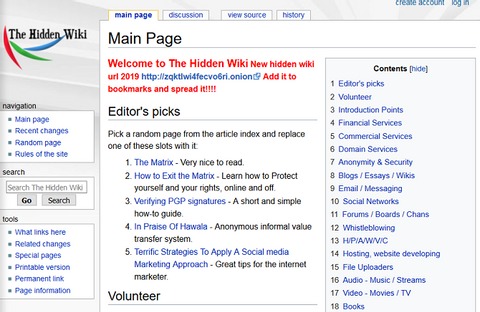
What Is The Hidden Wiki And How It’s Going In 2025?
- Specifically, the I2P darknet is accessible, while the Tor network is accessible through the Orchid Outproxy Tor plugin.
- In darknet mode, you can select friends on the network and only connect and share dark web content with them.
- But not to worry, any more, this list of the of the top 10 hidden Wiki alternatives will help you have a wonderful time of the dark web.
- Conversely, new platforms may emerge with transparent policies and robust security features, quickly gaining legitimacy through positive user experiences and community endorsements.
- Engaging in illegal activities (like buying drugs, weapons, or stolen data) is illegal.
- Yes, but you need to be cautious because there are many malicious sites on the dark web.
As the name suggests, this is a dark web alternative to the regular Wikipedia, which contains links to various websites found on the dark web. These “onion” sites are only accessible on the dark web and bear the “.onion” domain at the end of the URL. The websites on the dark web have the domain name ‘.onion’ as part of their URL. The dark web exists within the deep web and holds content that is accessible only using the Tor network. By leveraging such tools, businesses and governments can protect their data and communities from cyber actors.
- For example, a fake version of the Hidden Wiki might use a URL like hiddenwik1dotonion that instead of the real one, swapping one character to mislead users.
- Many deepweb platforms recommend or even require using metadata cleaners as part of their community rules.
- As a result, you should avoid opening unfiltered sources, torrent sites, and dark web links unnecessarily and downloading every file you come across.
- If you want to buy something on the dark web, it’s a best practice to create a fake identity.
- With this in mind, finding verified links is crucial for avoiding threats on the dark web.
- As the name suggests, Impreza Hosting is a (dark) web hosting service that provides all sorts of goodies such as domain names, host email services, and even servers for rent.
Is It Illegal To Access The Dark Web?
In combination with that data, and data gathered by other methods and/or tactics may in fact lead to complete exposure and could eventually lead to the police standing at your doorstep. If the product or service you’re attempting to buy is illegal, you’re running the risk of arrest. There’s a significant risk to dark web users of being exposed to malware (malicious software) infections.
It is essential to verify the links posted on it before you visit any, always. The website was subject to domain phishing in the past and runs on a centralized platform. Tunnels is ideal for those who want secure, private conversations online.
Always exercise extreme caution and verify the legality of any services you access. Using Tails OS can further security, as all your data is reset every time you close the device. A reliable VPN encrypts your traffic before it enters the Tor network, preventing surveillance from your ISP or malicious actors. BlackCloud offers encrypted file storage specifically optimized for the Tor network.
Verify All onion Links
Through APIs that feed alerts and risk scores into Security Information and Event Management (SIEM) tools. Credential leaks, ransomware campaigns, data broker listings, and emerging exploit kits. What types of threats are identified using dark web data? Yes, when conducted ethically under legal compliance and global data privacy frameworks. Is monitoring the dark web legal?
You can use Riseup on the regular internet or through the Tor network for extra privacy. Riseup is a secure email and chat service that doesn’t track or store your activity. It doesn’t censor out any content, so you’ll have free access to more than 400,000 indexed pages. It has some advertisements on its home page, but they’re for popular searches and services to help get you started. I like that it provides an option to report illegal content, such as child pornography or human trafficking.
DuckDuckGo’s no-track dark web search service can be accessed in the Tor browser and is an excellent resource for information about the dark web. There are multiple search engines on the dark web that can help you find what you’re looking for. There are a number of services and tools available on the dark web, many of which can be used for nefarious purposes. We’ve also previously mentioned the “dark users” that use the dark web for illegal reasons, but the less said about them, the better.

The same anonymity that publishers enjoy on the dark web can be utilized by users who want to read the available information. The dark web is a very popular platform for journalists, political bloggers and political news publishers, and in particular, those living in countries where censorship shields most of the internet. Naval Research Laboratory mathematicians and computer scientists in the mid-1990s. Social networks, such as Facebook, have created dark web versions of their sites to address privacy problems related to their surface web versions.
By leveraging layers of encryption, onion sites make it nearly impossible to trace the identity or location of either party. The .onion domain structure is designed to protect both the site owner and its visitors. Instead, you need specialized software, such as the Tor Browser, to access them securely. These sites are not accessible through traditional web browsers like Chrome or Firefox. Businesses must stay vigilant and proactive in addressing these threats, using tools like CybelAngel to monitor dark web activity and protect their assets. By providing real-time insights into threats, these tools enable companies to safeguard their brand and prevent data breaches before they occur.



