
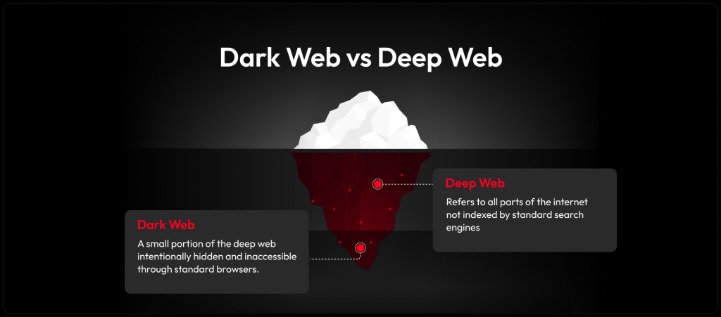
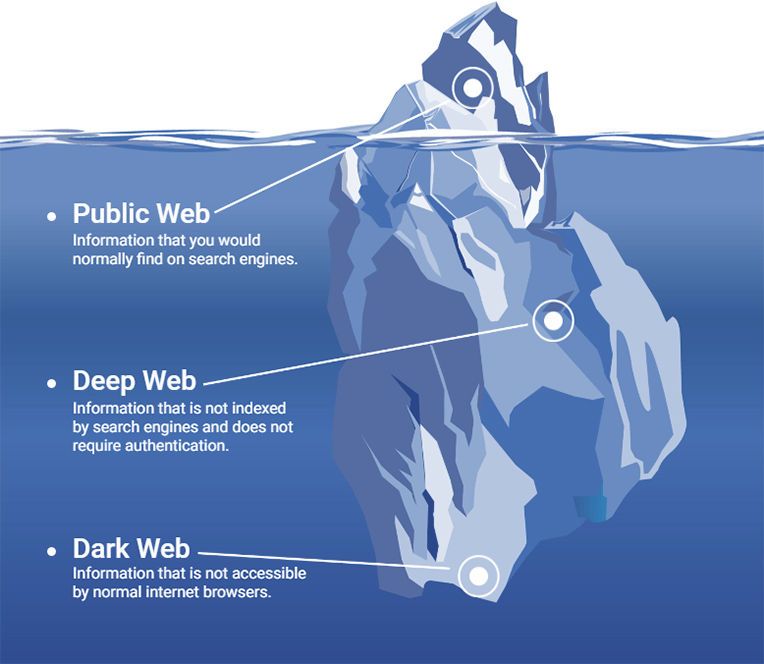
While it might sound daunting, following a few key steps can help you explore this hidden part of the internet without falling into its pitfalls. Think of it as the glossy shop windows of the internet — what you see is only what’s on display, neatly categorized and searchable. The dark web is like the mysterious basement of the internet — dimly lit, a little spooky and filled with stuff you probably shouldn’t touch. The Dark Web is an element of the internet that can only be accessed through specific software, such as Tor (The Onion Router), I2P (Invisible Internet Project), and Freenet.
In this article, we’ll take a look at how these tools work, how they differ from traditional search engines, and which dark web search engines are most widely used today. While traditional security tools focus on known threats, some of the biggest risks, like data breaches, identity theft, and corporate espionage, often start out on the dark web. It’s a hidden layer of the internet beyond the reach of traditional search engines. We have degree and certificate programs in Information Technology, Cyber Defense, and Cybersecurity Management that can teach you how to protect internet users online and prepare you for a number of rewarding career paths.
Forums cover the breadth of criminal activity but these examples show there is a particularly thriving community of cybercriminals sharing information, tutorials, access, and exploits. Dark web marketplaces offer mostly illegal products and services in exchange for payment. Our continuously updated content provides in-depth insights into marketplaces, ransomware actors, and hacking forums, helping you stay informed and proactively address challenges to safeguard your organisation or community. The Dark Web Hub equips law enforcement, enterprises, MSSPs, and researchers with essential knowledge to navigate dark web threats. Your connection also may be encrypted but if you do something like send an email from your personal account, then anyone with access to your inbox will know that you were online at that time.
Communication And Email
Regardless of being a business, parent, or any other user of the web, you’ll want to take precautions to keep your information and private life off the dark web. Some alleged services like the professional “hitmen” may just be scams designed to profit from willing customers. Infiltrations can put you at risk of monitoring for other types of activity as well. Even if you never make a purchase, you could be watched and incriminate yourself for other activities later in life. Any online activity can carry breadcrumbs to your identity if someone digs far enough.
FAQ: The Dark Web

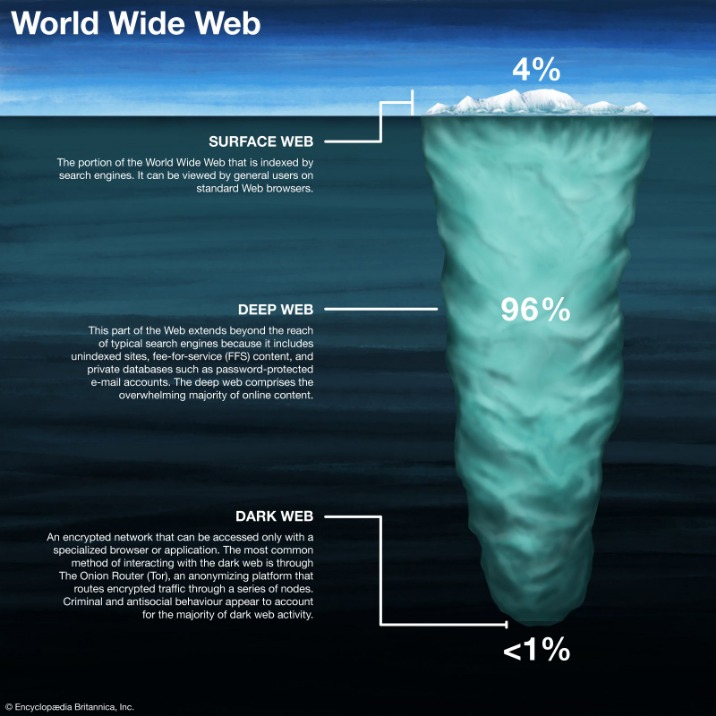
Many people see hacked information and stolen card data being sold on the dark web. Other sites explicitly block search engines from identifying them. You can access it with regular web browsers and search engines. As such, we do not recommend using Tor if you want to do data-intensive activities like streaming in HD, gaming, torrenting, or making video calls. The anonymity provided by onion routing comes at the cost of slowing your internet considerably. Many reputable websites and news outlets like ProPublica and SecureDrop often share official domain addresses of onion sites on their pages.
Do CISOs Need To Rethink Service Provider Risk?
In this article, we will unpack everything you should know about what the dark web is, how it works, how to surf it safely, and more. However, it also supports legitimate uses like protecting free speech and accessing information in censored regions. However, it's up to us to take control of our personal privacy in a world of bulk data collection, surveillance, and personalized ad tracking.
Legal Uses Of The Dark Web
The dark web is relatively small compared to the entire internet. When exploring the dark web, it’s crucial to exercise caution, as it’s not devoid of risks. By using a VPN, you can prevent eavesdroppers from intercepting your data when you’re connected to public Wi-Fi or any unsecured network. It allows you to mask your location and obscures your online activities, making it more difficult for cybercriminals to track you.

Many transactions conducted on the Dark Web involve the exchange of cryptocurrencies, as they offer a level of anonymity that traditional currencies cannot. By offering secure communication channels, it gives people in oppressive states the opportunity to connect with the outside world and engage in activism without facing the consequences of being identified. Activists in countries like China, Iran, and Russia use the anonymity provided by Tor to discuss sensitive political matters, organize protests, or disseminate information that might be suppressed by state authorities.
There’s nothing illegal about going on the dark web. This is where people buy and sell things—in this case, illegal stuff. From the ground up, there is plenty of disturbing content and information sitting on the dark web that you would not want to come across. Unfortunately, the same privacy and anonymity that protect lives and pure intents also cover up crimes and illegality. Despite the negative aspects, there are many people today who utilize the dark web for good, legal reasons.

How To Access The Dark Web On Desktop
The dark web refers to parts of the internet that aren’t indexed by standard search engines like Google or Bing. With rising curiosity around hidden corners of the internet, many professionals wonder, “how to access the dark web” safely. In 2002, the dark web grew significantly when researchers supported by the US Naval Research Laboratory built and released the Tor network. To check, you can use dark web scanning or breach detection tools like Avast Hack Check or LifeLock Breach Detection to search for compromised data. Regular dark web visitors know that it’s possible to exploit the sketchy reputation of the space and the services offered.
Defend Yourself Against Tracking And Surveillance Circumvent Censorship
- Most corporate and public sites work hard to make sure that these web crawlers can easily find them.
- And it supports the privacy needs of users for certain legal activities such as the exchange of proprietary business information.
- Understanding that the nature of the internet meant a lack of privacy, an early version of Tor was created to hide spy communications.
- Even if you’re a law-abiding citizen only looking to see what’s in the dark, hidden alleys of the internet, there are many dangers that can befall you.
- It is the dark web’s version of Wikipedia with a massive links directory.
It’s fitting because Tor itself stands for The Onion Router, a reference to the multilayered (like an onion’s skin) encryption it uses to keep users anonymous. When browsing through Tor on the dark web, however, the suffix is .onion. As we all know, websites on the surface web end with common suffixes such as .com, .org, .edu, and .gov. Department of Justice.3 The site became a hotbed for a range of unlawful goods and services, including illegal drugs and guns for hire.
What Is The Safest Way To Access The Dark Web?
- Although they all serve a similar purpose, these search engines differ significantly in terms of usability, safety features, and how they index content.
- Threat actors also exploit vulnerabilities in your systems and software to gain access to them.
- I personally recommend Tor over VPN because it’s the safer option — the VPN encrypts your traffic and changes your IP address, so the Tor network can’t see them.
- That means no one can access them but you — not even Proton.
Phishing schemes and fake escrow services are also common. You may encounter fake marketplaces promising illicit goods or services but delivering nothing after payment. As an average Internet user, you may accidentally stumble upon such content. In this article, we will explore the Tor dark web, referring to it simply as the dark web.
Find The onion Address You Want To Access
DefCon, ProPublica, the CIA, various libraries, and open-source software providers also feature in this area of the internet. The Tor network is operated by thousands of volunteers worldwide who maintain the proxy servers that protect your identity. You will need to visit the Tor Project to download the Tor Browser, a browser that prevents online fingerprinting, circumvents website blocks, and stops trackers from building a profile based on your browsing habits. ZDNET tested the best VPNs available based on speed, number of servers, security features, price, and more. The best VPN options are paid-for and subscription-based, as many free options will either throttle your speed or collect your data. A VPN will mask your location and stop the online breadcrumbs that can lead back to you.
Hackers sell access to email accounts, social media profiles, or other information that can be used for identity theft. Others sell software exploits that other cybercriminals can use to infect victims with malware and steal personal data. Because of the dark web’s association with illicit activity, your use of Tor may be tracked by your ISP, drawing unwanted scrutiny to your browsing behavior. And just like in real life, using the dark web for criminal purposes is never legal.
Best Dark Web Sites In 2025 + How To Stay Safe
Trained analysts may join forums or pose as buyers to access restricted conversations and inner circles. This supports damage control efforts and helps prioritize which systems, users, or customers require urgent remediation. When a breach occurs, the dark web can offer clues about the scope and source of the compromise. Knowing what attackers are buying, selling, or planning can guide the creation of threat models and inform security controls tailored to real-world risks. These insights allow security teams to better align their defenses with actual threats. Forums often contain discussions where attackers share tools, techniques, and procedures (TTPs), helping analysts profile adversary behavior.
Here are some of the ways to reduce the risks that come with using the dark web. The accuracy of search suggestions is another concern. Because it doesn’t use a crawler or ranking algorithm, OnionLinks is static and highly dependent on manual submissions, which makes it unreliable for current or time-sensitive research.



