
The anonymity provided by onion routing comes at the cost of slowing your internet considerably. This network of over 6,000 relays hides your location, thus protecting you from online surveillance and third-party tracking by your websites. Many reputable websites and news outlets like ProPublica and SecureDrop often share official domain addresses of onion sites on their pages. Although it’s no longer active, it’s setting the standard for coming onion links. This is the best place to get short and reliable links to an unalterable record of any webpage across government and corporate websites. However, data is required for understanding, monitoring, and improving the network.
The Hidden Wiki
While the best dark web sites listed above are a good starting point for a safe, legal surfing experience on Tor, there really is no substitute for a VPN. Enable MFA wherever possible to protect your accounts from unauthorized access. This adds another, more reliable security layer to all of your online activity. A VPN like Surfshark encrypts your internet connection and makes it harder for others to see your real IP address.
OnionLand Search
As you might expect, these websites sometimes host explicit, gory, harmful, and illegal content. In the internet's darkest corners, a myriad of hidden websites cater to an array of needs and interests. This enables individuals to form groups and only share content in a highly anonymous network of darknet users who they know.

Dark Web Search Engine
Telegram channels supplement traditional onion sites, blurring lines between the dark web sites and more mainstream communication tools. In some cases, it’s also used for private messaging, cybersecurity training, whistleblowing, and other legitimate uses. Dark web browsers and search engines do a lot of work to mask user identities, but you’re never completely untraceable. Typically, you can find dark web URLs through forums, databases, or by talking to others who frequent those sites. DuckDuckGo is built into the Tor browser, making it a convenient option for looking up dark web websites. Accessing content on the dark web takes a few extra steps, but it’s not as hard as you might think.
Media coverage typically reports on the dark web in two ways; detailing the power and freedom of speech the dark web allows people to express, or more commonly reaffirms the illegality and fear of its contents, such as computer hackers. Many journalists, alternative news organizations, educators, and researchers are influential in their writing and speaking of the dark web, and making its use clear to the general public. In 2015 it was announced that Interpol now offers a dedicated dark web training program featuring technical information on Tor, cybersecurity and simulated darknet market takedowns. Policing involves targeting specific activities of the private web deemed illegal or subject to internet censorship.
More Ways To Stay Safe On The Dark Web
There are a variety of private and encrypted email services, instructions for installing an anonymous operating system and advanced tips for the privacy-conscious. The Tor network began as an anonymous communications channel, and it still serves a valuable purpose in helping people communicate in environments that are hostile to free speech. We don’t want to leave you with the impression that everything on the dark web is nefarious or illegal.

The websites which can be accessed only over the Tor network have a ".onion" address. There are numerous directories that host .onion links and websites, but you should always exercise caution. Users can explore onion sites easily and search for content without having to know any specific onion links in advance. The New York Times operates one of the biggest news sites on the Tor network, letting users access its regular news coverage with increased privacy and security. Dark web websites are pages that exist on a part of the internet that isn’t indexed by traditional search engines like Google. Tor66 is a search engine catalog of dark web websites know as hidden services.
Understand Legal Risks
We continuously monitor and update our directories to minimize risks and ensure users have access to trusted, legitimate sites. The Hidden Wiki and its alternatives offer valuable gateways to deep web content that isn’t accessible through conventional search engines. It acts as a centralized hub to access sites that are not indexed by traditional search engines like Google. This directory focuses on providing users with verified, frequently updated links to a broad range of dark web services, including marketplaces, forums, and whistleblower platforms. Together, these technologies facilitate private, censorship-resistant access to hidden content, with the Hidden Wiki acting as a trusted directory to navigate this complex landscape. These tools enable users to connect to .onion or .i2p sites that exist outside the conventional internet infrastructure.
Risks That Dark Web Search Engines Pose
Needless to say, it takes your data much longer to travel this way, which means dark web links load slowly compared to indexed sites. Scroll on to learn more about dark web links (also called Tor links or onion sites), get the right links for some of the best Tor sites, and find out how to visit them safely. While you don’t need to log in to access any of the dark web links listed here, you can’t find them with a search engine like Google. Dark web search engines have become essential for enterprise security teams that need early … …More about Dark Web Search Engines in 2025 – Enterprise Monitoring, APIs and IOC Hunting The hidden wiki is an encyclopedia like Wikipedia, which is in the deep web, is one of the most complete guides to access the pages with onion links.
DuckDuckGo has a dark web version that is accessible through the Tor browser. Remember, though, that some of them provide no content filtering and may expose you to harmful content. Avoid sites that require JavaScript activation or make suspicious requests. These tools add layers of privacy and protect against data leaks and surveillance. Password managers can help manage your credentials without compromising security.
Ensuring The Security And Efficiency Of Web Applications And Systems
- It provides more privacy than regular search engines, but it mostly indexes the surface web and is not specialized for deep or dark web content.
- Besides monitoring and improving the network, the data can be used to detect possible censorship or attacks.
- We don’t want to leave you with the impression that everything on the dark web is nefarious or illegal.
- The New York Times operates one of the biggest news sites on the Tor network, letting users access its regular news coverage with increased privacy and security.
- However, these platforms often faced law enforcement takedowns, technical issues, or exit scams, where operators vanished with user funds.
- However, it's up to us to take control of our personal privacy in a world of bulk data collection, surveillance, and personalized ad tracking.
It hosted over 7,000 .onion categorized links to make surfing the web easier. Do you want to access the Onion sites with multiple devices? A budget-friendly VPN service allowing users to access dark web safely anytime, anywhere, and on any number of devices they want. It uses TrustedServer technology on the entire server network to wipe out your data after every session. Moreover, NordVPN is a service that doesn’t store or log your search results.
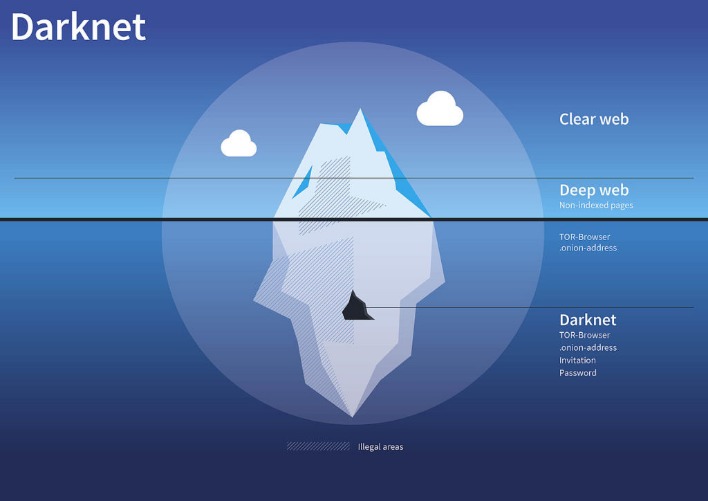
Tor is a network of volunteer relays through which the user’s internet connection is routed. It’s like an iceberg – The visible tip above water, known as the “surface web” represents the familiar, searchable content. Many mainstream media organizations monitor whistleblower sites looking for news. “A lot of people use it in countries where there’s eavesdropping or where internet access is criminalized,” Tiquet said. Nearly all dark web commerce sites conduct transactions in bitcoin or some variant, but that doesn’t mean it’s safe to do business there.
Cybercriminals often leverage the anonymity to leak sensitive information, like stolen credentials, credit card numbers, or company data. While it primarily indexes the surface web, it can also be accessed via the Tor browser and used as a general search engine. As a result, Torch is often considered one of the leading dark web search engines. It has a simple interface and is widely used for searching both legal and illicit content on the dark web. The problem is, the dark web isn’t indexed by regular search engines.
Many people use it for privacy-focused communication, whistleblowing, or accessing restricted information in censorship-heavy regions. The dark web is not exclusively used for illegal activities. However, while visiting the dark web itself isn’t against the law, engaging in illegal activities there is.
StrongBox adds advanced metadata stripping and encrypted messaging features, increasing whistleblower protection. GlobaLeaks is an open-source platform designed for NGOs and media to create customizable submission portals, emphasizing decentralization and anonymity. OnionShare is a popular open-source tool that allows users to share files securely and anonymously via Tor, widely used by activists and journalists for confidential document distribution. For developers and site operators, hosting on the dark web requires privacy, uptime, and resistance to attacks. These services form the communication backbone for sensitive conversations in high-risk environments. Sigaint provides encrypted email favored by whistleblowers and privacy advocates, focusing on ease of use and robust security.
Additionally, hidden wiki websites function as directories of categorized .onion links, providing common entry points for users delving into the hidden internet. At its core, the Hidden Wiki functions as a directory of .onion links — these are websites hosted on the Tor network, only accessible through the Tor browser. Hidden Wiki was originally the name of a .onion hidden service on the Tor network, hosting a directory for links to websites on the Tor dark web. Many dark web search engines offer uncensored search results, increasing the likelihood of encountering illegal content such as abuse material or hidden services. The Tor network adds a layer of anonymity, which helps dark web sites remain hidden and makes it impossible for conventional search engines to index them.
Some were taken down by law enforcement, others just vanished overnight with users’ money. The story of dark web marketplaces kicks off with Silk Road, launched in 2011. The first category includes classic marketplaces, which serve as one-stop shops for a wide range of illegal goods. Despite growing crackdowns from law enforcement agencies, the dark web remains a hotbed of criminal activity, offering everything from drugs to stolen data. However, it’s very difficult and would require extensive resources, meaning that the average person’s identity is unlikely to be uncovered. Once a buyer makes a payment, it’s usually held in escrow until they receive what they bought.
This is especially beneficial for professionals in cybersecurity or research, who require quick access to specific types of information. Dark web search engines are an alternative to having high technical knowledge, something hackers, journalists, and security firms are used to. That is why we emphasize caution, vigilance, and adherence to best security practices when exploring these hidden corners of the internet.



